Microsoft and Intel Enable AI-Backed Protection Against CPU Cryptocoin Mining
by Dr. Ian Cutress on April 27, 2021 7:10 AM EST
The fervor of cryptocoin mining has consumed a large part of the semiconductor industry of late. The demands for high performance silicon to mine these virtual assets with value is one factor in a global shortage of available parts for computers, automobiles, defense, research, and other industries. One consistent element to cryptocoin mining over the last decade is the prevalence of hijacked machines and devices through malware, commonly known as botnets. Previously these armies of machines were co-opted to perform bandwidth attacks against various targets, but they have also been used for their compute resources – mining coins that have value for those that control the botnet. This week Intel and Microsoft are announcing an additional layer of protection against these sorts of attacks.
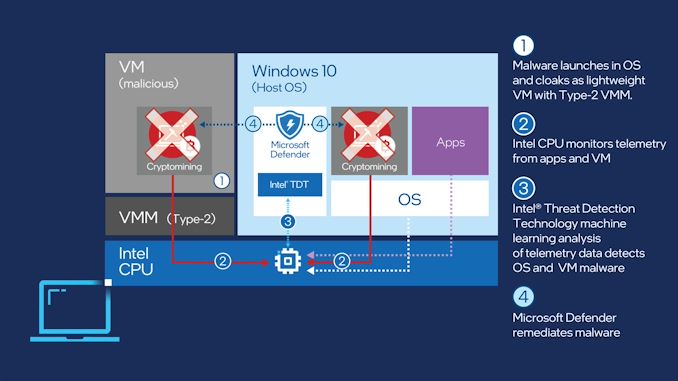
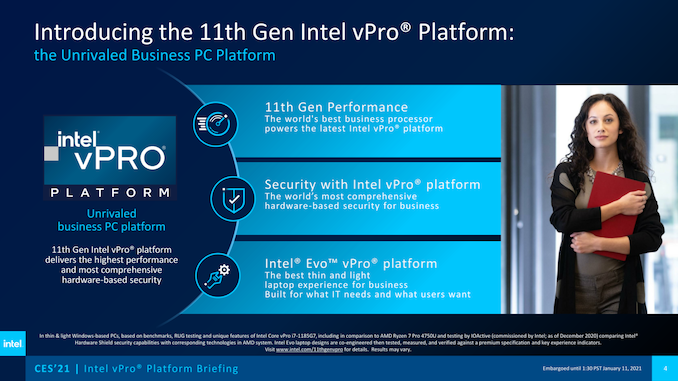
Commercial machines running Microsoft Windows, and managed through Microsoft Defender for Endpoint, can now be protected against CPU cryptocoin mining through an AI-backed protection mechanism. The security layer requires an Intel processor with Intel’s Hardware Shield (a vPro technology) and Threat Detection Technology enabled, which was introduced in 2018, and uses a combination of tools (such as CPU and GPU) to analyze the code being processed at a low level.
By performing consistent heuristic analysis through the CPU performance monitoring unit at a low level, the system can detect if it is mining without the owner’s consent. This can be detected either through a compromised hypervisor, virtual machine, or in the OS directly hidden as a separate process. If a threat is detected, an Endpoint detection and response solution is implemented to neutralize the mining utility, or quarantine it, and prevent the code from spreading across a network or fleet of managed systems.
Intel lists that over a billion CPUs can enable its Threat Detection Technology, from its 6th Generation processors onwards – Microsoft also highlights that Defender for Endpoint with TDT is supported on these systems. However both companies hide the fact in a footnote that the specific Cryptomining detection implementation is only possible on 10th Generation and newer platforms. It is also worth noting that this requires Intel’s Hardware Shield, which means vPro is also a requirement. So while there are a potential billion CPUs with some level of TDT in the market, this particular solution is only applicable to Windows based vPro machines managed at a corporate level. Still important, but not as big as the one billion number that Intel is promoting. Intel doesn’t list TDT as a feature on its main processor archive, ark.intel.com, either. It should also be noted that Intel TDT with memory scanning does consume integrated graphics resources to monitor the system – while this provides more power for CPU tasks, it undoubtedly raises the power consumption of systems when idle, which for mobile systems will reduce battery life. This is an ultimate tradeoff for security vs battery life.
Microsoft highlights that the ML-based technology used as part of TDT and Endpoint for Defender is a relative tip of the iceberg, providing a vehicle for more comprehensive protection against ransomware or side-channel attacks in future. These require pre-trained ML algorithms which Microsoft is currently working on and will roll-out as part of its Endpoint for Defender solution.
Despite the fact that low-end CPU cryptomining is not worth the effort for casual users, for those that control botnets of thousands of machines, it ends up earning them a few extra bucks using electricity they are not paying for, even in small IoT deployments such as security cameras. However there is a new class of cryptocurrency mining which is less compute reliant, and instead is storage based – the current system implemented by Intel and Microsoft seems to be focused on the current compute based cryptomining offerings. It will be interesting to hear if the new ML-based algorithms can also detect the newer coin types.
Related Reading
- Intel Launches 11th Gen vPro For Tiger Lake Mobile CPUs, Adds CET Security Tech
- “Microsoft Pluton Hardware Security Coming to Our CPUs”: AMD, Intel, Qualcomm
- AMD Issues Updated Speculative Spectre Security Status: Predictive Store Forwarding
- Hot Chips 31 Live Blogs: Intel/Tsinghua Xeon Jintide Security CPU
- BlackBerry Acquires Cylance, Gets AI & ML Security Technology
- Intel Announces Chip-Level Security Initiatives, iGPU-Based Malware Scanning











24 Comments
View All Comments
sonny73n - Wednesday, April 28, 2021 - link
I'm with you.Oxford Guy - Sunday, May 9, 2021 - link
You will never escape Google.Operandi - Tuesday, April 27, 2021 - link
Can this be turned off? Hopefully its not significant but it just sounds like my system level overhead that the enthusiast doesn't need running on their system.Also any chance of false positives with work loads from WCG or Folding@home? That would be supremely uncool.
Tomatotech - Tuesday, April 27, 2021 - link
It’s almost like you didn’t read the article, which carefully explains this is only available as part of an enterprise management system. If you own your own machine and it isn’t one of many thousands of computers belonging to a large corporation then this is unlikely to be available to you.Operandi - Tuesday, April 27, 2021 - link
Yeah I did read it, sorry that I don't know what "Microsoft Defender for Endpoint" is guess?And just because something is managed doesn't mean users can't install their own software on a device.
Tomatotech - Tuesday, April 27, 2021 - link
Imagine explaining to an AnandTech reader from 10 years ago that we now have AI routines operating without user permission to guard against crypto-mining botnets stealing CPU power, and that the environmental impact of crypto mining has become an issue of international concern.Farfolomew - Tuesday, April 27, 2021 - link
Those readers from a decade ago may not understand a single term you referenced, but I imagine their instincts would quickly be able to identify what they're feeling as something eerily familiar: a virus.Oxford Guy - Sunday, May 9, 2021 - link
'AI routines operating without user permission'Like anti-counterfeit stuff built into the very first inkjet printers?
Things like that are not new. What is new is the level of sophistication and connectivity.
grizewald - Tuesday, April 27, 2021 - link
I fail to see what this buzzword heavy "technology" brings to the table.You install a Microsoft/Intel BMC add-on and OS rootkit which runs at such a low level it can snoop into a VM. You also install a hidden, performance sucking ML inference system to process the data acquired. You have no certainty as to what data it reads and what it does with it - or where it sends it.
In return, you get some speculative warnings about a virus you may have caught.
Great idea! Just in time to boost new CPU, hardware and software sales by making most machines impossibly slow! Right in the middle of a global semiconductor drought! All prices are doubled! Profit!
If this is the best that Intel's new CEO can come up with, it really does not bode well for company's future.
Oxford Guy - Sunday, May 9, 2021 - link
'which runs at such a low level it can snoop into a VM'If you run closed-source software, don't expect the open-source experience.
If you run closed-source hardware...