The Intel SSD 910 Review
by Anand Lal Shimpi on August 9, 2012 1:00 PM EST- Posted in
- Storage
- SSDs
- Intel
- Intel SSD 910
The Drive and The Teardown
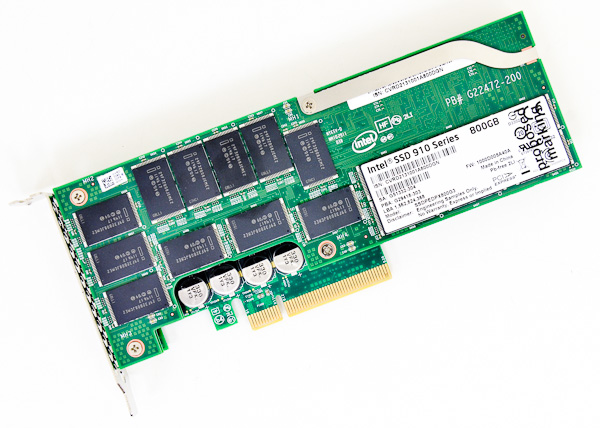
The 910 starts as a half height PCIe 2.0 x8 card, although a full height bracket comes in the box as well:
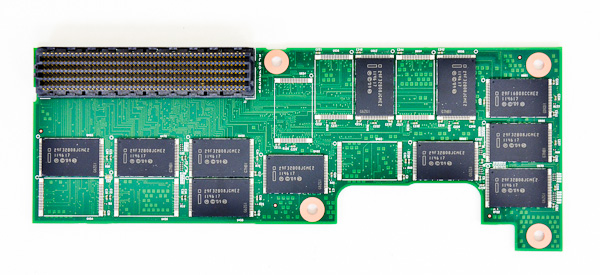
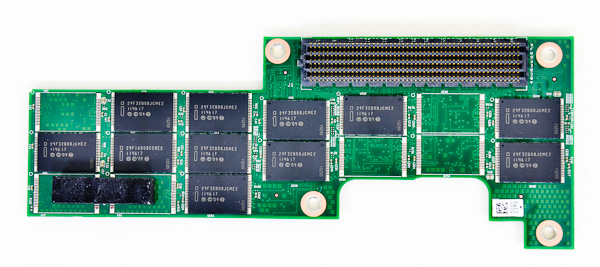
Intel sent us the 800GB 910, which features three total PCB layers that are sandwiched together. The 400GB model only has two boards. The top one/two PCBs (400GB/800GB) are home exclusively to NAND packages, the final PCB is where all of the controllers and DRAM reside. Each NAND PCB is home to a total of 28 NAND packages, for a total of 56 NAND devices on an 800GB Intel SSD 910. Here's a shot of the back of the topmost PCB:
Each PCB has 17 NAND packages on the front and 11 on the back. If you look closely (and remember Intel's NAND nomenclature) you'll realize that these are quad-die 25nm MLC-HET NAND packages with a total capacity of 32GB per package. Do the math and that works out to be 1792GB of NAND on a 800GB drive (I originally underestimated how much NAND Intel was putting on these things). Intel uses copious amounts of NAND as spare area in all of its enterprise class SSDs (the 2.5" 200GB Intel SSD 710 used 320GB of NAND). Having tons of spare area helps ensure write amplification remains low and keeps endurance high, allowing the 910 to hit Intel's aggressive 7 - 14 Petabyte endurance target.
| Intel SSD 910 Endurance Ratings | ||||
| 400GB | 800GB | |||
| 4KB Random Write | Up to 5PB | Up to 7PB | ||
| 8KB Random Write | Up to 10PB | Up to 14PB | ||
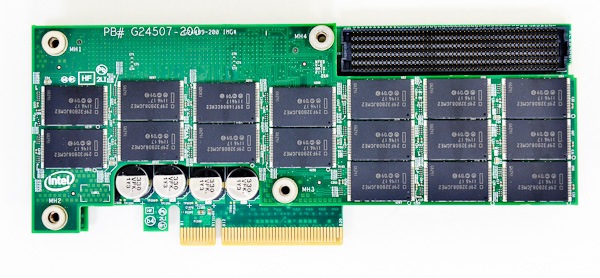
Remove the topmost PCB on the 800GB drive and you'll see the middle layer with another 28 NAND packages totalling 896GB. The NAND is organized in the same 17 + 11 confguration as the top PCB:
This next shot is the middle PCB again, just removed from the stack completely:
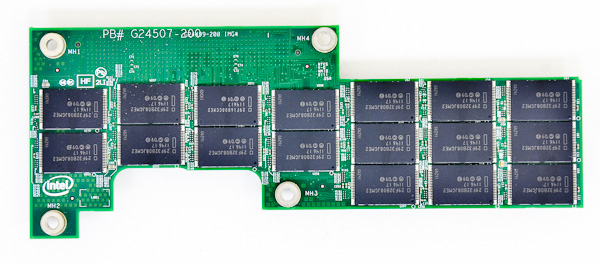
and here's the back of the second PCB:
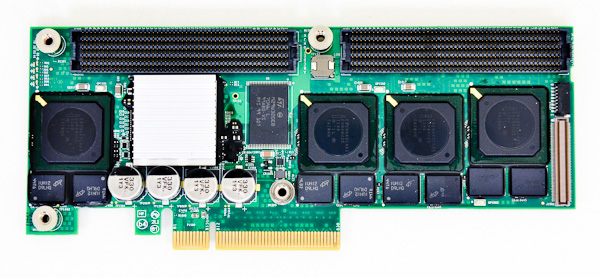
The final PCB in the stack is home to the four Intel/Hitachi controllers and half of the 2GB of DDR2-800:
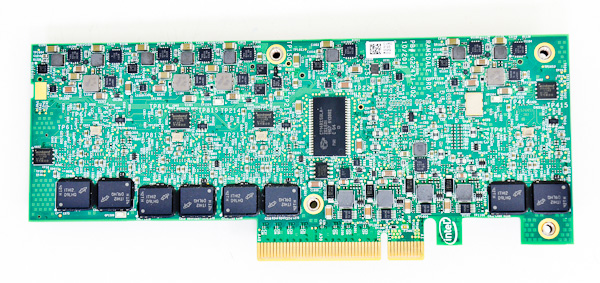
Under the heatsink is LSI's 2008 SAS to PCIe bridge, responsible for connecting all of the Intel/Hitachi controllers to the outside world. Finally we have the back of the Intel SSD 910, which is home to the other half of the 2GB of DDR2-800 on the card:
The 910 is a very compact design and is well assembled. The whole thing, even in its half height form factor only occupies a single PCIe slot. Cooling the card isn't a problem for a conventional server, Intel claims you need 200LFM of air to keep the 910 within comfortable temperatures.










39 Comments
View All Comments
Lazarus52980 - Thursday, August 9, 2012 - link
Wow, fantastic review. Thanks for the good work Anand.quiksilvr - Thursday, August 9, 2012 - link
Considering the hefty price on these devices, anything short of AES-256 in this day and age is unacceptable (yes I know you can do software encryption, but hardware accelerated is much more secure)prime2515103 - Thursday, August 9, 2012 - link
I'm confused. Isn't AES-256 the same whether it's done in hardware or software? I thought hardware encryption just performed better (encrypts/decrypts faster).Rick83 - Thursday, August 9, 2012 - link
AES-256 is no safer than AES-128, according to somewhat recent cryptanalysis on the algorithms.madmilk - Thursday, August 9, 2012 - link
Hardware acceleration is probably for performance, even AES-NI can't keep up with multiple PCIe SSDs.And yeah, AES-256 easier crack than AES-128 now. Not that it matters, with computational complexity still at what, 2^99?
It's much easier to just kidnap the sysadmin than attack crypto.
JPForums - Friday, August 10, 2012 - link
Since you didn't mention which attack you are referring to, I'm going out on a limb and assuming you are talking about the related key attacks on the full AES256 / AES192. I don't know of any other attacks that work on all 14 / 12 rounds. You should be aware that while such an attack is widely considered impractical, it isn't even possible under many circumstances. You need some up front data that you can't always get. To keep in relation to this article, I'll limit my scope to on the fly encryption software as it is closely related to the encryption implemented on this device. Several on the fly encryption packages are known to be immune to this kind of attack (I'll single out TrueCrypt as a popular open source package that isn't vulnerable to related key attacks). As long as you are using a properly programmed encryption package for your full disk encryption, AES-256 is still "more secure" than AES-128.
That said, if you actually calculated the amount of time it takes to brute force AES-128, you'll find that PCs and possibly humanity will have become a long forgotten relic of the past. Of course, processing power changes, but not that quickly. A bigger concern would be attacks that successfully bring the set of keys down to a manageable level. For this issue, diversity is probably more important than bit length, assuming the brute force key set is sufficiently large (I.E. 2^128).
Troff - Thursday, August 9, 2012 - link
I always end up needing to be able to communicate directly with each "drive", which is usually problematic through a raid controller and software raid is invariably faster and in every case I've tried so far much, much faster.Araemo - Thursday, August 9, 2012 - link
Isn't this necessary for trim anyways? If the OS can talk to each 'drive', trim should work, and performance will stay good, right?web2dot0 - Thursday, August 9, 2012 - link
Hey Anand,Shouldn't FusionIO cards be part of this comparison? It will most likely destroy the 910.
happycamperjack - Thursday, August 9, 2012 - link
http://hothardware.com/printarticle.aspx?articleid...Not according to this article. And ioDrive compared in this article is actually about 2x the price of either intel 910 or z-drive r4.