The Intel SSD 910 Review
by Anand Lal Shimpi on August 9, 2012 1:00 PM EST- Posted in
- Storage
- SSDs
- Intel
- Intel SSD 910
Intel's SSD Data Center Tool
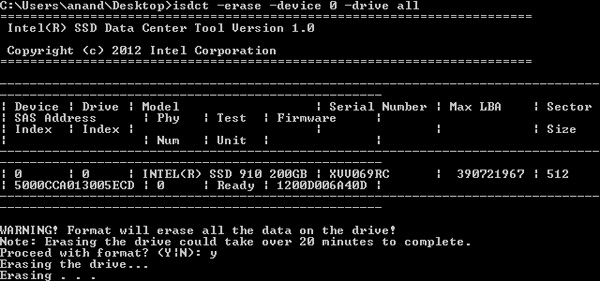
Despite Intel's wonderful desktop SSD toolbox, there's a more powerful but less user friendly option for the 910. It's called the Intel SSD Data Center Tool (isdct for short) and it's driven entirely by the command line. The tool is available for both Windows and Linux. You can use the isdct to secure erase the 910:
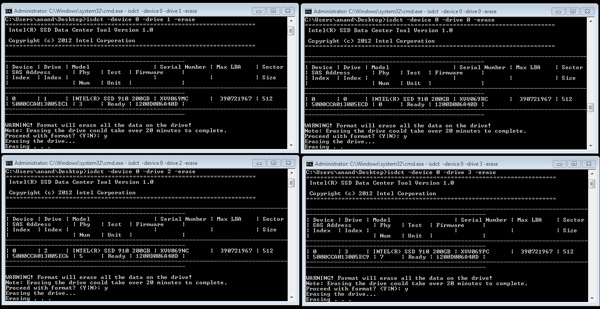
Each controller/partition must be secure erased independently, or in tandem by running four copies of isdct:
Since each partition is effectively an independent drive, you can run multiple isdct commands and just target a different drive with each instance. The isdct is also how you monitor temperatures on the individual drives, once again you have to execute a command per drive to get the temperature of that drive. Under Windows you need to execute the following command:
isdct.exe –log 0x2F –drive <drivenum> -device <devicenum> -verbose
Then look at the value of byte 10, which will tell you the current temperature...in hex. Convert back to decimal and you'll have the temperature of the specified NAND partition in degrees C. I have to admit I found all of this a bit endearing (I never get to read temperatures in hex), but your system administrator may be less impressed. Thankfully it shouldn't be all that difficult to script the isdct to quickly give you the data you want, even at regular intervals. The tool exposes quite a bit and since it's entirely command line driven it's pretty easy to automate, but I can't help feel like Intel should at least do some of this for you. I appreciate the flexibility, but others may want something a bit simpler.
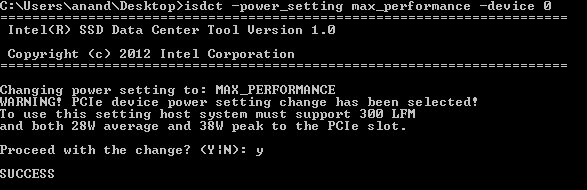
Other than obsessively monitoring temperatures (I never saw a temperature higher than 1F, 37 is the operational limit) and secure erasing the drives, I used the isdct to switch between performance modes on the 910:
Remember the 400GB drive always runs in this max performance mode, but the 800GB drive must be forced into it. You get a warning about the increased cooling and power requirements (up from 25W max TDP and 200 LFM cooling requirement) but otherwise the process is painless.










39 Comments
View All Comments
Lazarus52980 - Thursday, August 9, 2012 - link
Wow, fantastic review. Thanks for the good work Anand.quiksilvr - Thursday, August 9, 2012 - link
Considering the hefty price on these devices, anything short of AES-256 in this day and age is unacceptable (yes I know you can do software encryption, but hardware accelerated is much more secure)prime2515103 - Thursday, August 9, 2012 - link
I'm confused. Isn't AES-256 the same whether it's done in hardware or software? I thought hardware encryption just performed better (encrypts/decrypts faster).Rick83 - Thursday, August 9, 2012 - link
AES-256 is no safer than AES-128, according to somewhat recent cryptanalysis on the algorithms.madmilk - Thursday, August 9, 2012 - link
Hardware acceleration is probably for performance, even AES-NI can't keep up with multiple PCIe SSDs.And yeah, AES-256 easier crack than AES-128 now. Not that it matters, with computational complexity still at what, 2^99?
It's much easier to just kidnap the sysadmin than attack crypto.
JPForums - Friday, August 10, 2012 - link
Since you didn't mention which attack you are referring to, I'm going out on a limb and assuming you are talking about the related key attacks on the full AES256 / AES192. I don't know of any other attacks that work on all 14 / 12 rounds. You should be aware that while such an attack is widely considered impractical, it isn't even possible under many circumstances. You need some up front data that you can't always get. To keep in relation to this article, I'll limit my scope to on the fly encryption software as it is closely related to the encryption implemented on this device. Several on the fly encryption packages are known to be immune to this kind of attack (I'll single out TrueCrypt as a popular open source package that isn't vulnerable to related key attacks). As long as you are using a properly programmed encryption package for your full disk encryption, AES-256 is still "more secure" than AES-128.
That said, if you actually calculated the amount of time it takes to brute force AES-128, you'll find that PCs and possibly humanity will have become a long forgotten relic of the past. Of course, processing power changes, but not that quickly. A bigger concern would be attacks that successfully bring the set of keys down to a manageable level. For this issue, diversity is probably more important than bit length, assuming the brute force key set is sufficiently large (I.E. 2^128).
Troff - Thursday, August 9, 2012 - link
I always end up needing to be able to communicate directly with each "drive", which is usually problematic through a raid controller and software raid is invariably faster and in every case I've tried so far much, much faster.Araemo - Thursday, August 9, 2012 - link
Isn't this necessary for trim anyways? If the OS can talk to each 'drive', trim should work, and performance will stay good, right?web2dot0 - Thursday, August 9, 2012 - link
Hey Anand,Shouldn't FusionIO cards be part of this comparison? It will most likely destroy the 910.
happycamperjack - Thursday, August 9, 2012 - link
http://hothardware.com/printarticle.aspx?articleid...Not according to this article. And ioDrive compared in this article is actually about 2x the price of either intel 910 or z-drive r4.