AT&T 3G MicroCell: A Comprehensive Exploration
by Brian Klug on April 1, 2010 1:55 AM EST- Posted in
- Smartphones
- AT&T
- Microcell Review
- Mobile
What's going on inside?
In the spirit of really understanding how the AT&T MicroCell works, I was determined to get inside its inviting white shell. Unfortunately, after doing my homework, I started to get a feel for just how locked down this thing is - and why that's the case. First off, there's no internal status webpage as a diagnostic aide like you'd expect from a cable or DSL modem. Nothing. I searched around comprehensively for anything of the sort; it isn't there. What's surprising is that briefly, at startup, I saw nmap report ports 23, 80, and 8080 as filtered instead of open or closed, but that doesn't do anyone any good. The device always reports a hostname of "AT&T" and always pulls a DHCP lease at startup. There's no network configuration to speak of, so if you want to configure a static IP, static DHCP assignment is your only route.
Obviously, tech savvy users also are going to want to configure proper port forwarding and QoS rules for prioritizing MicroCell traffic. Unfortunately, documentation here is beyond spartan. There are (no joke) four versions of the users guide floating around. First is the printed copy in box, then there's an AT&T PDF, and finally one in the FCC filing - all of which lack the section on what ports should be forwarded. Curiously, there's another version online that I later found here with the relevant ports (on page 5), but this was after I had already discovered them on my own.
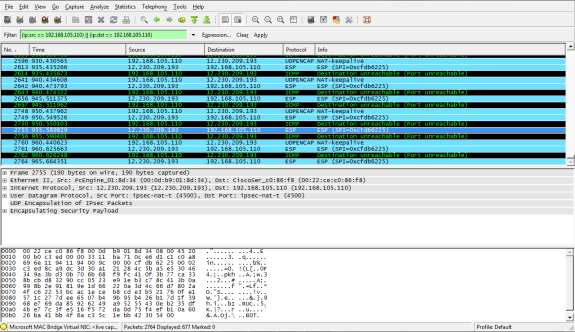
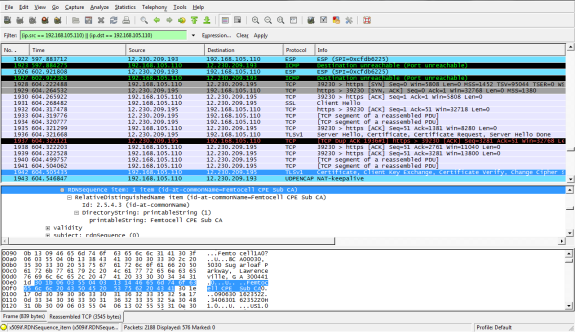
Before I stumbled across that real users guide, I was determined to find out how the MicroCell was talking with AT&T and over what ports. I grabbed a second NIC and set myself up in a machine-in-the-middle configuration and started sniffing packets. It's obvious immediately that this thing is locked down tight. After booting, the device grabs a DHCP lease, syncs network time over NTP with 12.230.208.48, and does a DNS query for dpewe.wireless.att.com. After it gets the results, it talks with that server over HTTPS (TLSv1) for a bit, and then immediately fires up an IPsec VPN with 12.230.209.193. After that, there's very little we can see going on - everything happens across that VPN tunnel.
Lots of IPsec traffic and NAT-keepalive
The MicroCell uses IPsec with NAT traversal, explaining partly why you don't really have to port forward, but it's still a good idea. In fact, it's during the HTTPS session certificate exchange that we see the only bit of network traffic which would lead us to believe this is a micro, er, femtocell:
So those ports that you should forward or prioritize if you're setting up QoS that way? They're here:
| Port | Description |
| 123/UDP | NTP Traffic |
| 443/TCP | HTTPS over TLS/SSL for provisioning and management traffic |
| 4500/UDP | IPSec NAT Traversal (for all signaling, data, and voice traffic) |
| 500/UDP | IPSec Phase 1 prior to NAT detection, after which 4500/UDP is used |










63 Comments
View All Comments
Some1ne - Thursday, April 1, 2010 - link
So let me get this straight. I'm supposed to pay AT&T for access to a device that uses my own Internet connection to patch up holes in their network? That's just ridiculous. It's AT&T's inadequate network coverage that makes these devices necessary in the first place, and now they're actually trying to profit off of having poor network coverage. Pretty much removes any incentive for them to improve their network, now doesn't it?These devices should be provided free of charge, as a "sorry you can't actually use the network that you paid to access" kind of token. Anyone who pays for one of these is just giving AT&T one more reason not to fix their coverage issues.
Alexstarfire - Thursday, April 1, 2010 - link
I rather agree. Makes you wonder what they actually do with all the money they receive monthly. Also means that if you purchase one, much like how it should be if you use an unlocked phone, that your monthly bill should drop in price. Except in this case if they are using your broadband connection then it should practically be free since it provides next to no burden on them, though I don't know what happens after it goes through the connection.therealnickdanger - Thursday, April 1, 2010 - link
How do you know that the actual cost of the device and the technology driving it isn't already subsidized by your bill? Perhaps you're only paying 10% of what it really costs.vol7ron - Thursday, April 1, 2010 - link
Even if a subsidy were included, which would only cover some (not all) of the costs, the fact that people have to pay anything more for it is ridiculous given the nature of what a cell company is: a service. Cell phone companies are in business for one reason and by making you pay anything more to receive the core product is truely sad.There are other companies, like Cisco, that have built their own repeaters and Mobile-to-VOIP products, which I commend, because they are a technology company not providing the service. They're taking something bad, that they don't have control of, and making it bearable. Cell phone providers are at the other end, they have full control but are making you pay more, even though you aren't getting the initial benefit of what you're paying for in the first place.
zinfamous - Thursday, April 1, 2010 - link
This is kind of where I sit with the argument. a one-time ~$150 cost to the customer *may* be cheaper in the end, than having a network-wide upgrade that increases costs across all customers, paying more and more per month.Perhaps it also improves access to those willing, and needing increased network performance, paying a bit more for the premium, while those customers with little need for the bandwidth go on about their normal use, paying what they always have. It's like...a single-payer network structure! :D
DoeBoy - Thursday, April 1, 2010 - link
IT seems to me some people forget that companies are in business to make money. This is a great way for ATT to make a lot of extra money. I live in a rural area and i complain all the time in an area they say has coverage that does not at all. While this would aid me in getting better service it also would require me to pay for an inet connection which is not covered by att. Clearly they aren't a moral company when your service is so bad you have to have a product that uses some other technology(a la internet) and then charge the person not only for that product that gets you service but not even lower your bill since you technically arent using their towers really at all under this sucker. Clearly Verizon and ATT are both big 500lb gorillas. In europe its much easier to get a cheap cell phone deal and coverage. Clark Howard seems to think ATT and Verizon are going to end up being more corporate and smaller companies like t-mobile, cricket, metropcs and what not will fill in the void for the regular consumer.Some1ne - Thursday, April 1, 2010 - link
The problem is that when you look at the pricing matrix, not only is there a fixed upfront cost, there are also recurring monthly fees. It doesn't matter how much the up front cost is subsidized. The monthly fees mean that sooner or later, AT&T will be turning a profit on these devices.And even worse, the fees are higher if you're not already using AT&T as your ISP and/or land-line provider. That makes the least sense out of anything, since if you have a different ISP, then by running the femtocell you are completely unburdening AT&T's network, and dumping all the work onto someone else. The get to sell your bandwidth to someone else, and charge you more while doing it.
taltamir - Thursday, April 1, 2010 - link
in computers, the technology is made mostly of sand... it costs practically nothing.It is the technology you are paying for...
However there is one major component here, AT&T themselves look at it as a "cost cutting method"... in other words it is intended to cost them LESS, aka, they are making MORE of a profit on you if you get one of those then without.
The whole thing is absurd. You pay hundreds of dollars for a black box device with tamper protection and absolutely horrid performance (compared to wifi), then you pay a monthly fee for the privilege of using said device...
they should just put wifi in every device and have wifi be free (but they usually charge a monthly fee for that privilege as well)
ant1pathy - Friday, April 2, 2010 - link
You are, of course, welcome to change carriers. If you feel the service you are recieving is subpar and another carrier would be better for you, the termination fee is probably less than the cost of the box. If you're continuing to pay for a service that does not meet your needs and you can't really use, then you are the pefect consumer.Wolfpup - Wednesday, April 21, 2010 - link
I completely agree. It's absolutely nuts IMO.