Hot Chips 2018: Microsoft Azure Sphere Live Blog (5:30pm PT, 12:30am UTC)
by Ian Cutress on August 20, 2018 8:18 PM EST
08:18PM EDT - For the security section of Hot Chips, the first talk is from Microsoft on their Azure Sphere, which is an end-to-end solution for securing microcontroller powered devices with the cloud.
08:19PM EDT - We're starting early
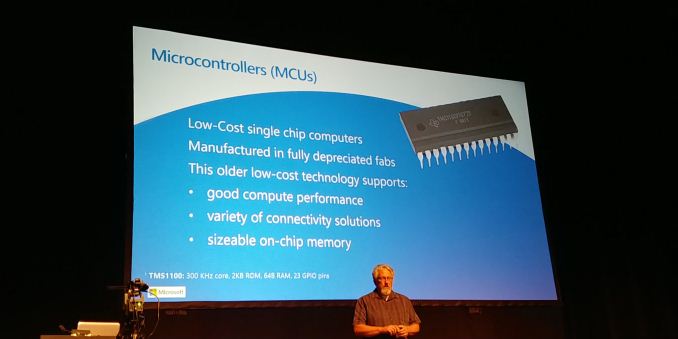
08:19PM EDT - Azure Sphere is about microcontrollers
08:20PM EDT - MCUs are used everywhere
08:20PM EDT - Don't require massive processing - most are not even 32-bit devices
08:20PM EDT - low cost, older fabs
08:20PM EDT - Those old fabs now offer a wide variety of performance and connectivity and on-chip memory
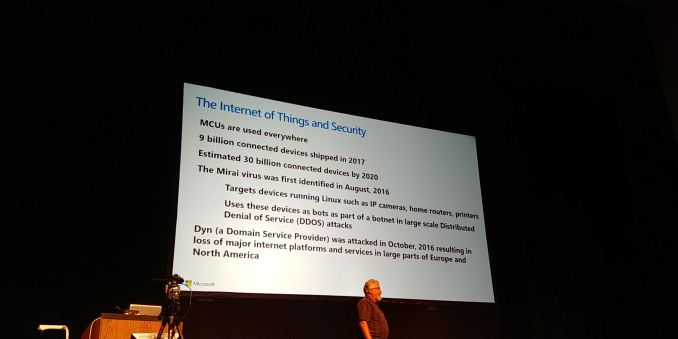
08:21PM EDT - 9b connected devices shipped in 2017
08:21PM EDT - Large attack surface
08:22PM EDT - Only required 100k devices with Mirai to cripple services
08:22PM EDT - Azure sphere requires a sphere classified MCU
08:23PM EDT - Uses MS OS on the MCU for security
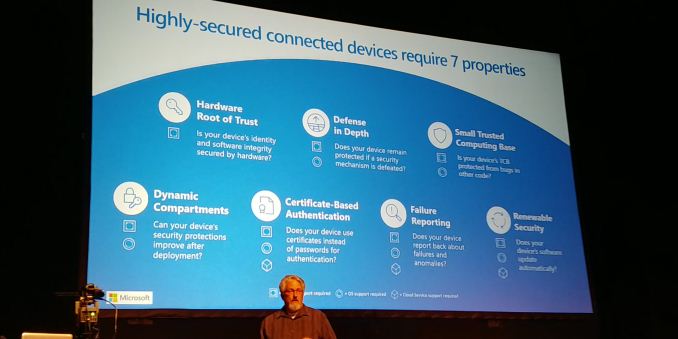
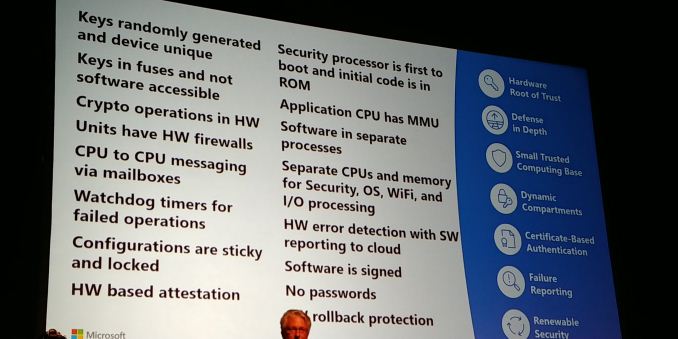
08:24PM EDT - Hardware has to participate in security
08:24PM EDT - each device has to have a unique ID
08:24PM EDT - no one security measure is bulletproof
08:24PM EDT - ensure one feature doesn't reveal all the secrets
08:24PM EDT - security code has to be small and contained and protected
08:25PM EDT - compartments for code
08:25PM EDT - managing the code space
08:25PM EDT - certificates for security
08:25PM EDT - Azure Sphere MCUs don't use passwords
08:25PM EDT - people don't change root passwords
08:25PM EDT - generate device specific certificates for cloud service authentification
08:25PM EDT - means of failure reporting
08:25PM EDT - also needs to be updateable
08:26PM EDT - no point having devices that can't be updated
08:26PM EDT - Need to do it securely
08:26PM EDT - Need to ensure older softeware can't run
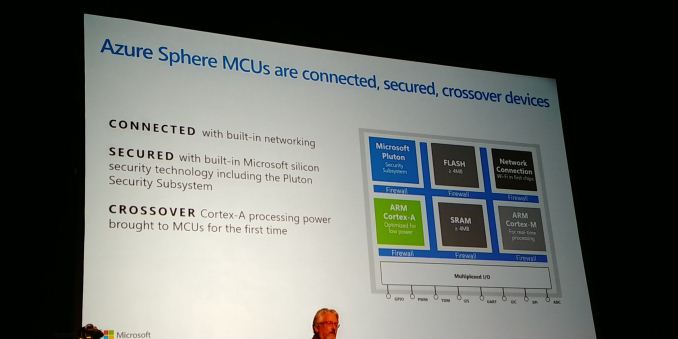
08:27PM EDT - Most MCUs that exist are low cost, scalar. For Azure Sphere, need processor with an MMU
08:27PM EDT - Needed to isolate processes
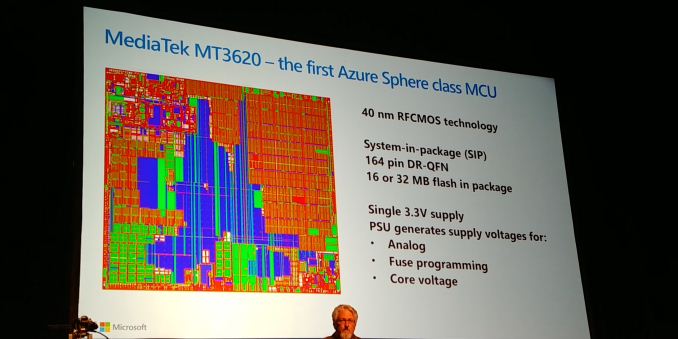
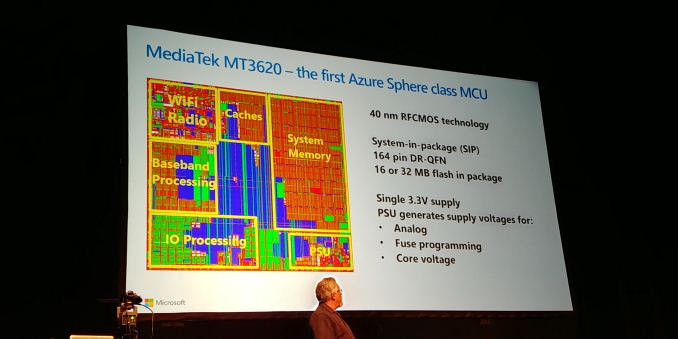
08:28PM EDT - First Azure Sphere MCU is 40nm process from Mediatek, 300m SRAM transistors (most of them)
08:28PM EDT - SiP, two flash die in package
08:28PM EDT - low cost plastic package
08:28PM EDT - single 3.3V supply - all other voltages handled on chip
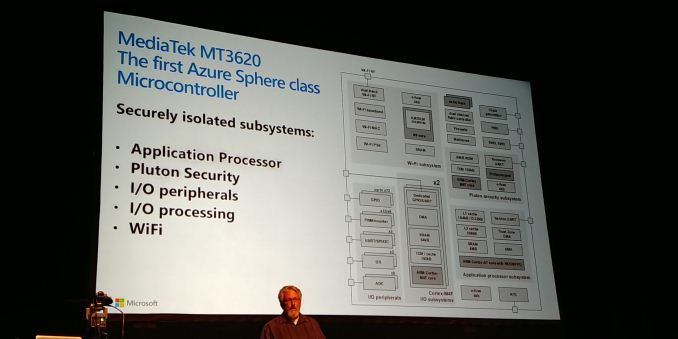
08:29PM EDT - 5 main processing systems on chip
08:29PM EDT - Microsoft Pluton security core
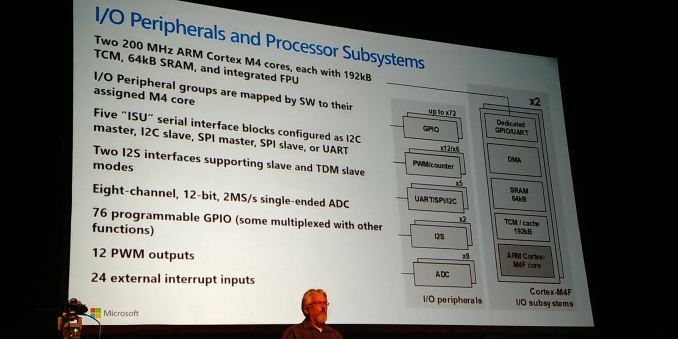
08:29PM EDT - Cortex M4F for IO
08:30PM EDT - WiFi up to 802.11n, dual band
08:30PM EDT - 1T/1R
08:30PM EDT - Uses N9 32-bit RISC core
08:30PM EDT - Chip wasn't targeted at a particular system, so a fairly standard chip with collection of IO
08:31PM EDT - Plenty of flexibility
08:31PM EDT - Analog sampler
08:31PM EDT - I2C, SPI, UART, GPIO, PWM outputs, external interrupts
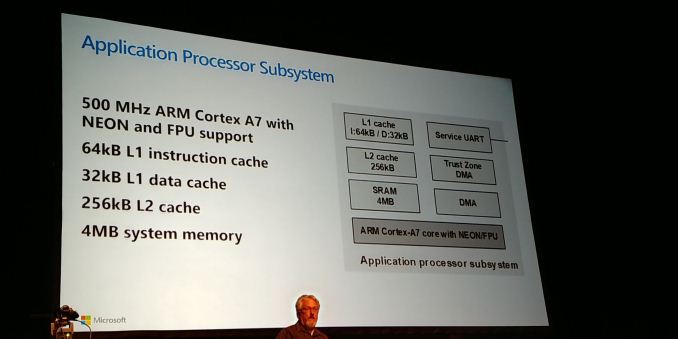
08:32PM EDT - OS runs on Cortex A7 at 500 MHz
08:32PM EDT - Neon/FPU present
08:32PM EDT - 4MB system memory
08:32PM EDT - OS runs almost completely in memory
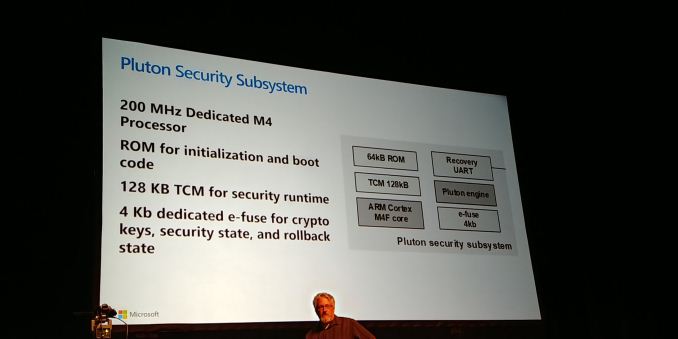
08:32PM EDT - Pluton is the security subsystem
08:33PM EDT - 200 MHz M4 processor, uses ROM for initialization
08:33PM EDT - ROM does cert validation of security code
08:33PM EDT - Runs all code local out of coupled 128kB
08:33PM EDT - Dedicated e-fuse macro
08:34PM EDT - stored in a fashion where hardware can use them but software can't read them
08:34PM EDT - Stores security state in e-fuse
08:34PM EDT - rollback protection fuses so older software doesn't run
08:34PM EDT - Pluton is Microsoft IP
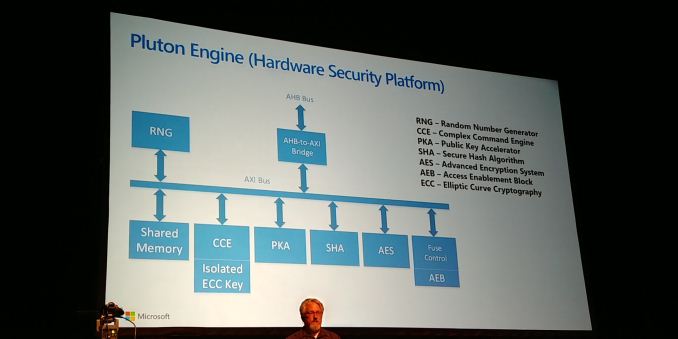
08:35PM EDT - Has all control features for keys and fuse bits
08:35PM EDT - Private/public chip key pair generated on chip
08:35PM EDT - SHA and AES engines
08:36PM EDT - List of features (not all of features)
08:37PM EDT - Every unit in the device has a firewall
08:37PM EDT - Can isolate every device to its own memory region
08:37PM EDT - Configuration bits are sticky - can be set on boot and can't be edited except at boot if required
08:39PM EDT - Internal OS based on Linux
08:40PM EDT - Time for Q&A
08:41PM EDT - Q: Any plans to open source the Pluton core? A: Software will be open source, hardware will be royalty based
08:42PM EDT - Q: Who owns the root key in a distributed product? A: Depends what you mean. for the OS, Microsoft. For the application it's the manufacturer.
08:42PM EDT - Q: No way for the user to restrict silent updates? A: Not in the plans today, aside from disconnecting the device.
08:44PM EDT - Q: How you plan to provision these devices? Instrastructure? A: That infrastructure exists today. Provisioning such as certificates happens as a co-op process between IC manufacturer and Microsoft. It works with the cloud as it is manufactured. It's unique to the chip, based on the public key.
08:46PM EDT - Q: In the history, companies with new MCU architectures tend to have trouble. What's MS' background? A: We didn't do any new instruction sets. The processors are made by Arm and Andes N9. There's no new extensions here.
08:48PM EDT - Q: Can you disclose any physical adjustments made to protect side channel attacks? A: We can't talk much about what's done in hardware. Can say that we do restrict the keys, and side channels go after that - the hardware means attacks don't have the same opportunity to attack crypto engines to extract those keys.
08:49PM EDT - Q: The PSU is on chip. Are there multiple power domains? A: Yes, portions of the design can be shut down as needed. Revalidation occurs on power cycles, not power down of separate domains
08:51PM EDT - Q: Infrastructure is built around IP from Arm and Andes. Are you agnostic - are you happy to work with RISC-V etc? A: We're not completely committed to cores, that was just used with Mediatek based on experience. We will look into support, depending on our team
08:51PM EDT - Q: What's the power consumption of that Mediatek chip? A: We focused this chip on wall-connected devices, not battery, but it does have a super low power mode of 7 micro-watts. Normal power can be as high of 600 mW. Without Wi-Fi it's about 200mW.
08:52PM EDT - That's a wrap. Next talk is on Google Titan. https://www.anandtech.com/show/13248











2 Comments
View All Comments
tobats120 - Thursday, August 23, 2018 - link
Wondering why MS would use chinese chip if they're talking about securityDigi07 - Monday, November 2, 2020 - link
i love reading your blogs as i mostly get the valuable information from your site and one another site naming Janbask Training