ioSafe 1513+ Review: A Disaster-Resistant Synology DS1513+
by Ganesh T S on August 13, 2014 7:30 AM EST- Posted in
- NAS
- Storage
- Synology
- Enterprise
- ioSafe
Chassis Design and Hardware Platform
The Synology DS1513+ has been around for more than a year now. ioSafe announced the disaster-resistant version back at CES and tentatively set the shipment date for March. However, it wasn't until late July that the design was finally perfected. Compared to the SoloPRO and the ioSafe 214 platforms, the 1513+ is quite different when it comes to power consumption and thermal requirements. Tackling the heat dissipation was one of the main challenges faced by ioSafe in the product development process.
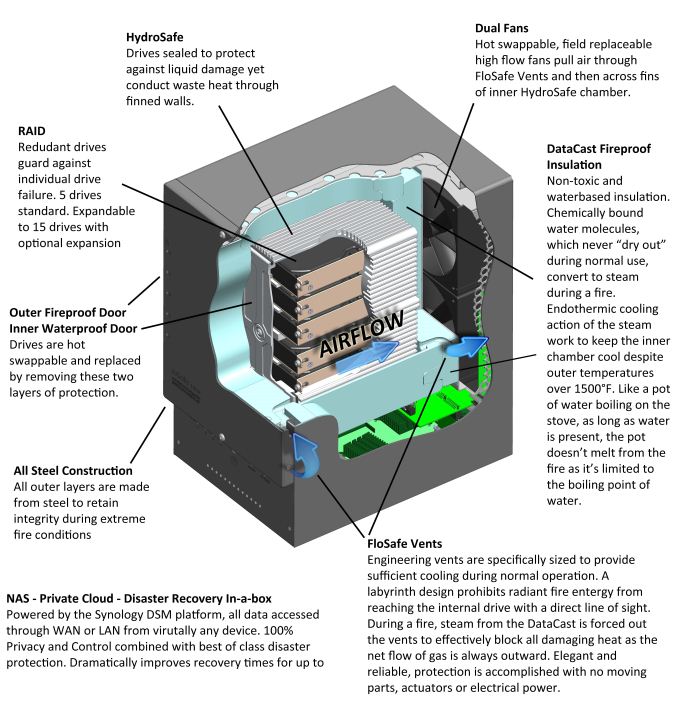
ioSafe uses three main patented technologies in disaster-proofing the 1513+:
- HydroSafe: Waterproofing by placement of drives in a metal cage sealed with rubber gaskets.
- DataCast: Fireproofing by surrounding the drive cage with a super-saturated gypsum structure
- FloSafe: Vents in the gypsum structure to allow for cooling during normal operation.
ioSafe has a technology brief explaining how these are applied in the 1513+. It is reproduced below:
In traditional NAS units / storage arrays, the arrangement of the fans has to ensure that air flows across the surface of the drives in order to cool it down. This is not directly possible in the ioSafe NAS designs because the hard drives are inside a waterproof sealed chamber. Ambient air is not designed to enter the waterproof chamber, but, through the fireproof door and to the outside of the extrusion. For cooling purposes, the design relies on a combination of conduction (from the drives to the extrusion) and convection (from the extrusion to the ambient air flowing over the extrusion). Note that the waterproof front door of the drive cage as well as the fireproof front face are essential parts of the cooling mechanism. Without these, the airflow across the serrated drive cage might not be enough to draw away the heat through the fans.
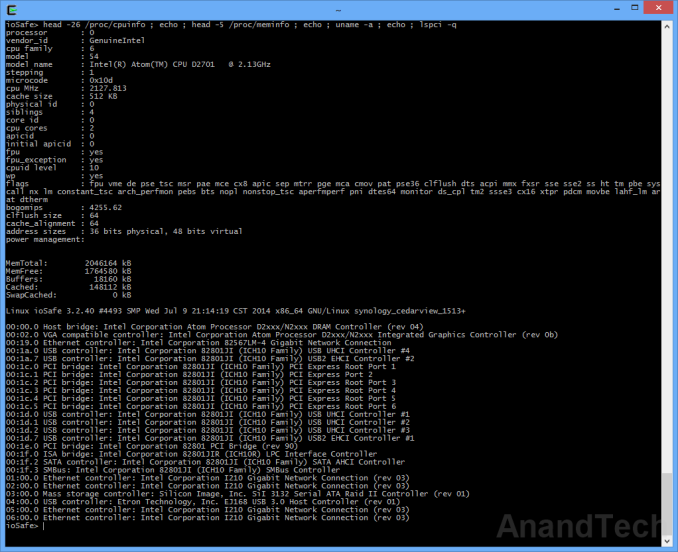
On the software front, the ioSafe 1513+'s Synology DSM is based on a Linux kernel (v 3.2.40). The interesting aspects of the hardware platform can be gleaned after accessing the unit over SSH.
Note that the unit has four Intel I210 GbE NICs connected via PCIe. The USB 3.0 ports are from an Etron EJ168 PCIe x1 to 2x USB 3.0 bridge,while a SiI 3132 PCIe x1 to 2x eSATA host controller with port multiplier support enable the two eSATA ports (to which the expansion chassis units get attached). Since the system utilizes the ICH10 I/O controller hub (this is the standard Cedarview storage platform that Intel promoted a few generations back), all the SATA ports for the drive bays come off the hub without the need for any bridge chips.
Our review unit came with the drives pre-initialized in a SHR volume (1-disk fault tolerance). ioSafe has a special wallpaper for the web UI, but, other than that there is no customization - all DSM features that one might get after initializing the unit from a diskless configuration are available in the pre-installed version also.
We have covered DSM 5.0's setup and usage impressions in our recent DS214play and DS414j reviews. There is not much point in rehashing the same excellent setup and usage experience. That said, each of those reviews concentrated on a particular DSM aspect, and this review will be no different. After the sections presenting the performance numbers, we will take a detailed look at the iSCSI features of DSM 5.0.










43 Comments
View All Comments
jmke - Wednesday, August 13, 2014 - link
ioSafe is the 3rd party backup copy;1st onsite, 2nd offsite, 3rd copy on the ioSafe.
with almost everything digital, the ioSafe is the equivalent of a... safe :) a high quality classic "fire and waterproof" safe will set you back ~$500-600. Add in the cost of the DS513+ and you get where the price comes from...
if you can backup offsite reliably! then surely do, ioSafe offers an alternative solution, never bad to have other options :)
robb.moore - Thursday, August 14, 2014 - link
Thx jmke. With this particular system (especially setup on HA), it's viable for many SMB's that the 1513+ be used as primary and maybe glacier or another offsite service be used for maybe a smaller set of tier1, hyper critical files. It's possibly the best of all worlds for RPO/RTO, cost, etc. And if a backhoe takes out your internet connection, you haven't lost all DR capabilities.Robb Moore, CEO
ioSafe Inc.
Gonemad - Wednesday, August 13, 2014 - link
Add some layers of kevlar, a spring-mounted cage, and a internal UPS that calls for 5-minutes safe shutdown. Bulletproof, explosion resistant, power outage resistant. Or shove it in a safe for good measure. I bet there is a market for it. If you change the drives to flash ones, you get even better explosion resistancy.DanNeely - Wednesday, August 13, 2014 - link
Where are the grill/swimming pool tests?romrunning - Wednesday, August 13, 2014 - link
Ganesh, did you check to see if this "disaster-resistant" Synology make-over is also "resistant" to SynoLocker (i.e., patched against it)? Someone encrypting all of my files would certainly qualify as a disaster to me! ;)ganeshts - Wednesday, August 13, 2014 - link
Our review unit came with DSM 5.0 installed, so that is immune to the SynoLocker exploit.That said, the lesson from the SynoLocker episode for me was that we might be better off not exposing the unit to the Internet at all. We might end up losing a lot of nice features of DSM, but I think it is worth the peace of mind. In addition, security vulnerabilities exist everywhere. Today, Synology has been exploited - tomorrow, it might be some other NAS vendor.
I also suspect that the use-case for ioSafe 1513+-like devices involves storing of sensitive data - no IT admin in his right mind would leave ports open from such devices for access from an external network. It would probably be through a VPN or something similar.
romrunning - Wednesday, August 13, 2014 - link
Sadly, I know of some "admins" who do not have the same regard for security. To them, it is just about reacting to the latest request, like "I want to access my files from home and everywhere else". They open it up, and then leave the default basic authentication as-is.From experience, I would wager the percentage of those types of admins are a bit higher than you might expect of such a position.
gizmo23 - Wednesday, August 13, 2014 - link
LACP: I thought we moved on to 802.1X about 5 years agobobbozzo - Wednesday, August 13, 2014 - link
Something this big would quickly bake if you had it running in a sealed safe.jay401 - Friday, August 15, 2014 - link
Is it also EMP proof? :)