ioSafe 1513+ Review: A Disaster-Resistant Synology DS1513+
by Ganesh T S on August 13, 2014 7:30 AM EST- Posted in
- NAS
- Storage
- Synology
- Enterprise
- ioSafe
Chassis Design and Hardware Platform
The Synology DS1513+ has been around for more than a year now. ioSafe announced the disaster-resistant version back at CES and tentatively set the shipment date for March. However, it wasn't until late July that the design was finally perfected. Compared to the SoloPRO and the ioSafe 214 platforms, the 1513+ is quite different when it comes to power consumption and thermal requirements. Tackling the heat dissipation was one of the main challenges faced by ioSafe in the product development process.
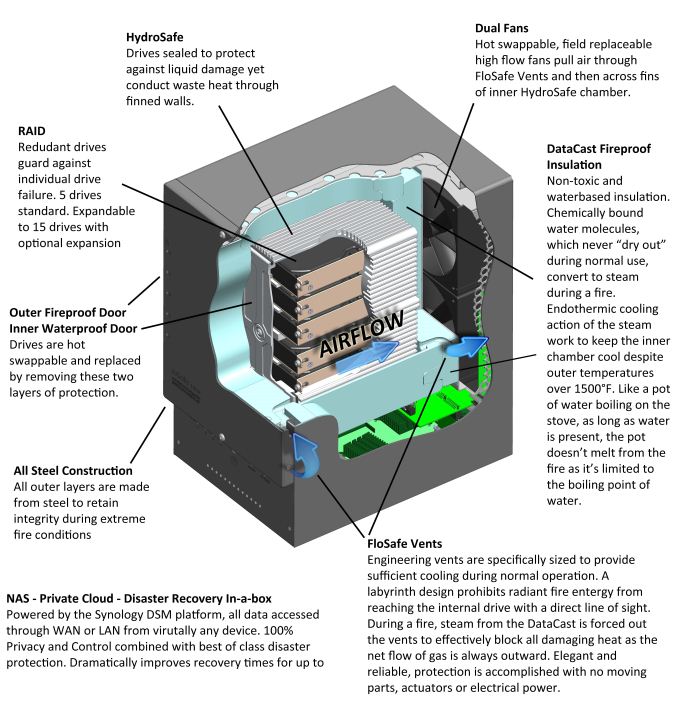
ioSafe uses three main patented technologies in disaster-proofing the 1513+:
- HydroSafe: Waterproofing by placement of drives in a metal cage sealed with rubber gaskets.
- DataCast: Fireproofing by surrounding the drive cage with a super-saturated gypsum structure
- FloSafe: Vents in the gypsum structure to allow for cooling during normal operation.
ioSafe has a technology brief explaining how these are applied in the 1513+. It is reproduced below:
In traditional NAS units / storage arrays, the arrangement of the fans has to ensure that air flows across the surface of the drives in order to cool it down. This is not directly possible in the ioSafe NAS designs because the hard drives are inside a waterproof sealed chamber. Ambient air is not designed to enter the waterproof chamber, but, through the fireproof door and to the outside of the extrusion. For cooling purposes, the design relies on a combination of conduction (from the drives to the extrusion) and convection (from the extrusion to the ambient air flowing over the extrusion). Note that the waterproof front door of the drive cage as well as the fireproof front face are essential parts of the cooling mechanism. Without these, the airflow across the serrated drive cage might not be enough to draw away the heat through the fans.
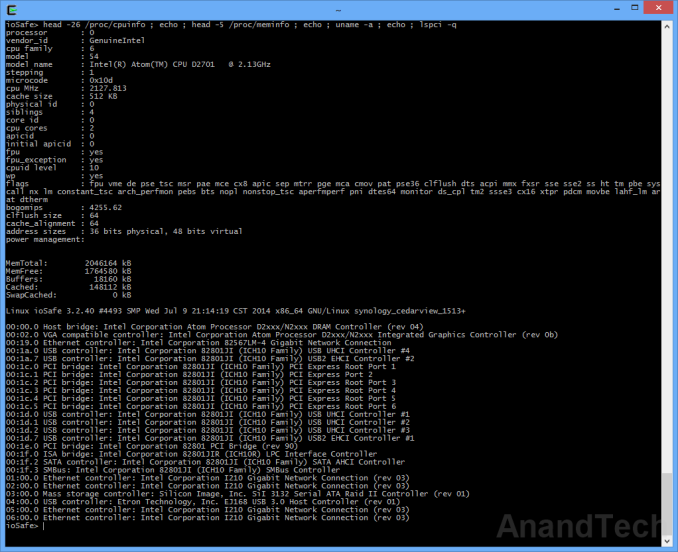
On the software front, the ioSafe 1513+'s Synology DSM is based on a Linux kernel (v 3.2.40). The interesting aspects of the hardware platform can be gleaned after accessing the unit over SSH.
Note that the unit has four Intel I210 GbE NICs connected via PCIe. The USB 3.0 ports are from an Etron EJ168 PCIe x1 to 2x USB 3.0 bridge,while a SiI 3132 PCIe x1 to 2x eSATA host controller with port multiplier support enable the two eSATA ports (to which the expansion chassis units get attached). Since the system utilizes the ICH10 I/O controller hub (this is the standard Cedarview storage platform that Intel promoted a few generations back), all the SATA ports for the drive bays come off the hub without the need for any bridge chips.
Our review unit came with the drives pre-initialized in a SHR volume (1-disk fault tolerance). ioSafe has a special wallpaper for the web UI, but, other than that there is no customization - all DSM features that one might get after initializing the unit from a diskless configuration are available in the pre-installed version also.
We have covered DSM 5.0's setup and usage impressions in our recent DS214play and DS414j reviews. There is not much point in rehashing the same excellent setup and usage experience. That said, each of those reviews concentrated on a particular DSM aspect, and this review will be no different. After the sections presenting the performance numbers, we will take a detailed look at the iSCSI features of DSM 5.0.










43 Comments
View All Comments
ddriver - Saturday, August 16, 2014 - link
Thanks for the input. BTW, where I come from, "cellar" does not imply "basement" - our cellars are usually on floor levels, tiny room, around 1 m^2 for general storage purposes, no water mains no nothing. Closer to what you may call "pantry" in the US. Cultural differences... me'h. Nothing to burn and nothing to flood in there. Plus noise in the cellar bothers nobody.Never failed a demo - which exactly proves the point I make earlier about being careful with controlled fires. That would create the illusion your products are flawless and someone's gonna buy one expecting it to survive his fancy wooden and lacquer soaked cottage burning to the ground which I am willing to bet it will not. You should really draw the line between "office fire accidents" and "fire disasters" just for the sake of being more realistic and not deceiving consumers, deliberately or not. People are impressed by big numbers, and could easily be impressed by the 1700 F number, absent the realization most flammable materials burn at significantly higher temperatures. Every engineer knows - there is no such thing as a flawless product, the fact you never had a failed demo only goes to show you never really pushed your products. With those zero failed demos you will very easily give consumers the wrong idea and unrealistic expectations, especially ones who are not educated on the subject. You SHOULD fail a few demos, because it will be beneficial for people to know what your products CAN'T HANDLE. A few failures in extreme cases will not degrade consumer trust as your PR folks might be prone to believing, it will actually make you look more honest and therefore more trustworthy.
ddriver - Saturday, August 16, 2014 - link
I mean better you cross that line with a test unit than some outraged consumer going viral over the internet how your product failed and he lost his life work ;)robb.moore - Monday, August 18, 2014 - link
Hi ddriver-As mentioned, our fireproof tech relies on proven methods that are over 100 years old. Appreciate the heated skepticism though. As an engineer myself, I agree that no product is flawless and everything (including our own products) have their limits. I take back the "never failed a demo" comment. We did some gun demos with shotguns (passed) - got a bunch of flack for ONLY using shotguns so we redid the demo with fully auto AR-15's - blew holes completely through the product and of course failed...sometimes. Fun demo though.
-Robb
Phil Stephen - Monday, August 18, 2014 - link
ddriver: I'm a firefighter and can confirm that, based on the specs, these units would indeed withstand a typical structure fire.zlobster - Sunday, August 17, 2014 - link
Dear Mr. Moore,I'm really glad that you actually follow up with the public opinion.
I'll try to use the opportunity and use it to ask you whether you are planning to build a unit with non-Intel CPU, rather with AMD/ARM/Marvell/etc.? A unit that can handle the latest industry standards for on-the-fly encryption without sacrificing the performance even a bit?
Also, besides the physical integrity and resiliency tests that you are conducting, do you do similar penetration-testing for data integrity? I mean, with well-known independent hacker/pen-testing communities? With all the fuzz around govt. agencies putting backdoors virtually everywhere, it's of extreme importance for the piece of mind of extreme paranoics (like me), to know how hack-proof your devices are.
Regards,
Zlob
robb.moore - Monday, August 18, 2014 - link
Hi Zlop-We're constantly working on new products. The 1513+ does use an Intel chip but our other NAS (2 bay), ioSafe 214 uses a Marvell chip. We realize that encryption can be important in many situations and we're always interested in balancing features, cost and speed for our products. Can't make direct comments though on what we have in the pipeline except stay tuned! :)
In regards to "hack-proof", the most "hack-proof" systems (aka CIA, etc.) don't exist on the internet at all. They're fully contained offline in secured facilities. In fact, ioSafe systems are used in situations like this where offsite backup (online or physical relocation) is not allowed or impractical but the end user still wants a disaster plan.
Obviously, there's a balance between security, accessibility, cost and speed. If you put an ioSafe system online, no firewall, never update OS/firmware, all ports open with standard admin passwords - expect mayhem. If you put an ioSafe system in a bank vault, offline and turned off it's obviously pretty secure but inaccessible - not very useful. Security can be complicated. Striking the right balance is different for every situation. Our NAS systems are based on the Synology platform which in turn is a custom Linux kernel so it's as safe as you make it generally (like all connected systems) and is susceptible to hackers if setup incorrectly. We're very happy to help you with configuring your device if you have any questions at all about the tradeoffs.
Ultimately though its under your control. You're in charge of opening or closing doors.
Robb Moore, CEO
ioSafe Inc.
PEJUman - Saturday, August 16, 2014 - link
I second that, for this price... I really want to know it it would last the rated time under fire. Should try it under propane {bbq tank 2300+ C} and and Nat. Gas/wood based flame {1900+ C} To simulate household/industry gas line.bsd228 - Thursday, August 14, 2014 - link
Well for the $1000 extra, one could buy a 30"x72" inch gun safe that can also be used to store the regular Synology (or a DIY NAS) plus guns, camera gear, and any other valuables. Harder to steal as well- they weight 500-1000lbs.DanNeely - Thursday, August 14, 2014 - link
Maybe; but good luck using the NAS with the door shut...smorebuds - Thursday, August 14, 2014 - link
l0l