In-Depth with the Windows 8 Consumer Preview
by Andrew Cunningham, Ryan Smith, Kristian Vättö & Jarred Walton on March 9, 2012 10:30 AM EST- Posted in
- Microsoft
- Operating Systems
- Windows
- Windows 8
Windows Recovery Environment
The Windows Recovery Environment, or WinRE, has actually been around for awhile. It was first introduced in Windows Vista as a basic boot environment from which users could run tools like System Restore, Startup Repair, and the Command Prompt, and it could also restore a complete OS image created by Windows Backup.
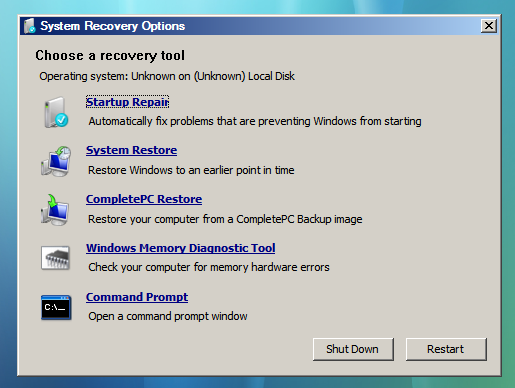
This menu remained basically unchanged in Windows 7, but in Windows 8 it picks up Metro styling and also replaces the text-based menu that appears when you press F8 at Windows startup, one of the last bastions of the Windows 9x/NT era to make it into 2012 relatively unchanged.
The new graphical menu presents all of the same options as the old WinRE, as well as access to the new Refresh and Reset functionality—the main difference is that options for booting into Safe Mode are buried in the Advanced Options rather than coming up right when you press F8. When you choose a function like System Restore, the desktop-style tools included in Windows Vista and Windows 7 will pop up and walk you the rest of the way through the process. Most of the troubleshooting options require you to input the name and password for an administrator on the computer, to prevent tampering.
There’s nothing groundbreaking here, but the Metro styling is functional and attractive. See the screenshot gallery below for more.
Secure Boot and UEFI Support
After Metro, this is probably one of Windows 8's more misunderstood features, so let's try to break it down and demystify it: UEFI (Unified Extensible Firmware Interface) is a replacement for the legacy BIOS found in most PCs. UEFI support has been around in the 64-bit versions of Windows since Vista, but it has only recently started to see wider adoption in PCs. In addition to being more modern and flexible than BIOS, UEFI supports a feature called Secure Boot, which can compare signatures in drivers, OS loaders, and other things against security certificates stored in firmware to verify that your computer is using a known safe bootloader rather than a malware bootloader. On both ARM and x64 computers certified for Windows 8, Secure Boot will be enabled by default to prevent these potential exploits. Note that this is an extremely brief overview of the functionality—you can read more on the Building Windows 8 blog if you’re interested.
Now, the problem people have with this new feature is that it can potentially be used to block any non-Windows bootloader from functioning, including those used in operating systems like Linux. By default, this is true, but you’ve got an out: in all x86-based Windows systems that ship with Windows 8, you should be able to add and remove security certificates from UEFI as needed (thus adding certificates that Linux needs to be recognized as a trusted operating system) or disabling secure boot entirely (making the Windows 8 PC act more or less like most Windows 7 PCs do now).
This will be slightly different for Windows on ARM—WOA systems will also support UEFI and thus the Secure Boot feature, but users won’t be allowed to add certificates or disable the feature, and OEMs will be disallowed from shipping updates or tools that unlock the bootloader (as some Android tablet makers have been known to do). You might not like this behavior, but the fact remains that this is how the vast majority of ARM devices work today. Linux advocates act as though Microsoft has taken something away in disallowing third-party OSes on WOA devices, when in fact they’re disabling nothing that hasn’t already been disabled on most competing tablets.
















286 Comments
View All Comments
yannigr - Friday, March 9, 2012 - link
This is more of a funny post but.... do you hate AMD systems? Are AMD processors extinct? I mean 8 systems ALL with Intel cpus? Come on. Test an AMD system JUST FOR FUN..... We will not tell Intel. It will be a secret. :pGothmoth - Friday, March 9, 2012 - link
AMD?who is still using AMD?
except some poor in third world countrys?
no.. im just joking... AMD is great and makes intel cheaper.. if only they would be a real competition.
but what about ARM?
that would be more interesting.. but i guess we have to wait for that.
JarredWalton - Friday, March 9, 2012 - link
In defense of Andrew's choice of CPU, you'll note that there's only one desktop system and the rest are laptops. Sorry to break it to you, but Intel has been the superior laptop choice ever since Pentium M came to market. Llano and Brazos are the first really viable AMD-based laptops, and both of those are less than a year old. AFAIK, Andrew actually purchased (or received from some other job) the laptops he used for testing, and they're all at least a year old. Obviously, the MacBook stuff doesn't use AMD CPUs, so that's three of the systems.As for the two laptops I tested, they're also Intel-based, but I only have one laptop with an AMD processor right now, and it's a bit of a weirdo (it's the Llano sample I received from AMD). I wouldn't want to test that with a beta OS, simply because it's likely to have driver issues and potentially other wonkiness. Rest assured we'll be looking at AMD systems and laptops when Win8 is final, but in the meantime the only thing likely to be different is performance, and that's a well-trod path.
DiscoWade - Friday, March 9, 2012 - link
Last year, I needed to buy a new laptop. I wanted a Blu-Ray drive and a video card. I thought I would have to settle for a $1000 computer with an Intel processor. I had narrowed my choices down to a few all with the Intel i-series CPU. When I went to test some out at Best Buy, because I wanted to play with the computer to see if I liked it, I saw a discontinued HP laptop on sale for $550. It was marked down from $700. It had the AMD A8 Fusion CPU and a video card and a Blu-Ray drive. So I got a quad-core CPU with 4 hour actual battery life that runs like a dream very cheap. I was a little apprehensive at first with buying the AMD CPU, but a few days of use allayed my fears.If you say Intel makes better laptop CPU's, you haven't used the AMD A series CPU. It has great battery life and it runs great. How often will I use my laptop for encoding video and music? The dual-AMD graphics is really nice. Whenever I run a new program, it prompts which graphic card to use, the discrete for power savings or the video card for maximum performance. I like that.
Yes if I wanted more power, the Intel is the way to go. But my laptop isn't meant for that. And most people don't need the extra performance from an Intel CPU. Every AMD A8 and A6 I've used runs just as good for my customers and friends who don't need the extra performance of an Intel.
However, I haven't yet been successful installing my TechNet copy of W8CP on this laptop. I'm going to try again this weekend while watching lots of college basketball. (I love March Madness!) If anybody can help, I would appreciate if you let me know at this link:
http://answers.microsoft.com/en-us/windows/forum/w...
MrSpadge - Friday, March 9, 2012 - link
You do realize that Jared explicitely excluded Llano and Brazos from his comment? A8, A6, A4 - they're all Llano.Samus - Monday, March 12, 2012 - link
I'm actually shocked he didn't use an AMD E-series laptop (HP DM1z, Lenovo x120/x130, etc) as they have sold hundreds of thousands in the last 12 months. I see a DM1z every time I'm in an airport, and x120's are very commonplace in education.Remembering the Sandybridge chipset recall last year, this really gave AMD a head start selling low power, long battery life laptops, and they have sold very well, and belong in this review when you consider the only laptops you can buy new for <$400 are AMD laptops, and that is a huge market.
silverblue - Monday, March 12, 2012 - link
This isn't a review. Also, he didn't have one.Quite open to somebody benching a DM1z on W8CP, though. ;)
phoenix_rizzen - Friday, March 9, 2012 - link
While Intel may have the better performance CPU in laptops, they have the *worst* (integrated) graphics possible in laptops, and have 0 presence in the sub-$500 CDN market.You'd be surprised how many people actually use AMD-based laptops, especially up here in Canada, mainly for three reasons:
- CPU is "good enough"
- good quality graphics are more important than uber-fast CPU
- you can't beat the price (17" and 19" laptops with HD4000+ graphics for under $500 CDN, when the least expensive Intel-based laptop has crap graphics and starts at over $700 CDN)
frozentundra123456 - Friday, March 9, 2012 - link
A bit confused by your post. What is HD 4000 graphics? Granted Llano is superior to SB, but Llano is 66xx series isnt it? I though AMD 4000 series was a motherboard integrated graphics solution that is very weak. Intel SB graphics will be far superior to any integrated solution except Llano.I agree for my use, I would buy Llano in a laptop ( and only in a laptop) because I want to do some light gaming, but I dont understand your post. I would also not really call SB graphics "crap" unless you want to play games.
inighthawki - Friday, March 9, 2012 - link
HD 4000 is referring to the intel integrated graphics on the new ivy bridge chips - nothing to do with AMD chips