AMD 2013 APUs To Include ARM Cortex-A5 Processor For TrustZone Capabilities
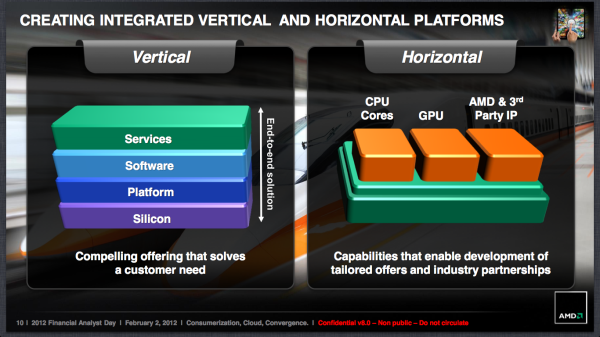
by Ryan Smith on June 13, 2012 8:00 AM ESTAt AMD’s 2012 Financial Analyst Day, as part of their presentation on their future strategy AMD’s CTO Mark Papermaster announced that AMD would be looking into integrating 3rd party IP into future AMD APUs. At the time there was a strong assumption that this would be mobile focused – perhaps in the form of a cellular modem or an ARM core – and it turns out the assumptions were both right and wrong. Today AMD is announcing that they are in fact going to start integrating ARM cores into future APUs starting in 2013, but not in the way you’re probably thinking.
If you look at AMD’s long term strategy, not only do they need to continue to compete with Intel on the technology front, but they also want to better position themselves to compete on the tablet front. AMD has the basic hardware for this with their APU families, particularly for tablets with their Zacate based entry-level APUs, but they have a feature gap in certain markets. Both Intel and ARM have hardware trusted platform/security technologies but AMD lacks such a technology.
For various reasons we’ll get to in a moment, AMD believes they need some kind of hardware security platform technology to continue to compete in the market in the future. Intel’s Trusted Execution Technology is not part of the x86 specification and is therefore not shared, so AMD would need to come up with their own technology. Designing and implementing such a technology is not only resource intensive but by its very nature it fragments the market, which is something AMD doesn’t necessarily have the clout to get away with all the time. So rather than design their own technology they’ve chosen to license an existing technology, and this brings us to ARM.

In order to implement a hardware security platform on their future APUs, AMD has chosen to enter into a strategic partnership with ARM for the purpose of gaining access to ARM’s TrustZone technology. By licensing TrustZone, AMD gains a hardware security platform that’s already in active use, which means they avoid fragmenting the market and the risks that would bring. Furthermore AMD saves on the years of work – both technical and evangelical – that they would have needed had they rolled their own solution. Or more simply put, given their new willingness to integrate 3rd party IP, licensing was the easy solution to getting a hardware security platform quickly.
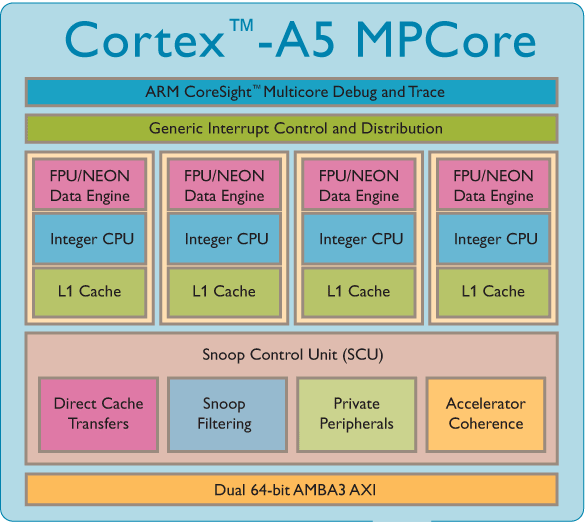
But because TrustZone is an ARM technology (both in name and ISA) AMD needs an ARM CPU to execute it. So the key to all of this will be the integration of an ARM processor into an AMD APU, specifically ARM’s Cortex-A5 CPU. The Cortex-A5 is ARM’s simplest ARMv7 application processor, and while it’s primarily designed for entry-level and other lower-performance devices, as it turns out it fits AMD’s needs quite nicely since it won’t be used as a primary application processor.
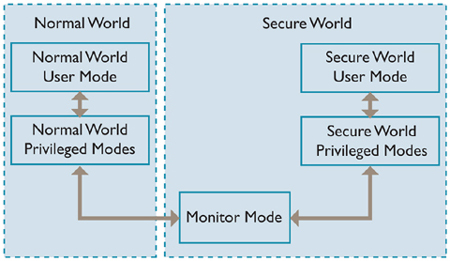
ARM TrustZone Hardware Model; Normal World Would Be On x86
This also means that the ARM and x86 CPU cores will fit together in an interesting manner unlike any existing ARM or Intel x86 CPU. By integrating a low-power/low-performance ARM CPU in this manner an application will be split up over multiple CPUs, with the TrustZone secure backend executing on the Cortex-A5 while the frontend logic will be executing as normal on AMD’s x86 CPU and GPU cores. This gives AMD a dedicated security co-processor with all the benefits and drawbacks thereof, while on full ARM processors and on Intel’s x86 processors TrustZone and TXT respectively are hardware features of a single CPU.
By implementing a hardware security platform in this manner AMD not only gains a relatively quick turnaround time on the hardware, but on the software side too. AMD is specifically looking to leverage existing ARM applications for their tablet ambitions by taking advantage of the fact that existing TrustZone application cores can easily (if not directly) be ported over to AMD’s APUs. Developers would still need to put in some effort to write the necessary x86 frontends (in all likelihood written in scratch for Win8 as opposed to any kind of Android), but the hard part of implementing and validating the TrustZone functionality would simply carry over, leaving the new x86 frontend to talk to the existing ARM TrustZone application core. AMD isn’t in any position to talk about specific software yet, but we’re told that they’ve been working with select software partners even before this announcement in order to get a jump on developing applications.
As for the hardware details AMD hasn’t named any specific APUs that will be receiving the Cortex-A5, but they have told us that they intend to start with the low-power APUs in order to go after the tablet market. That means we’re almost certainly looking at the 2013 successor to the Zacate APU found at the heart of AMD’s Brazos platform. However AMD won’t be stopping there, and in 2014 and beyond AMD will continue to add it to further APUs until AMD’s entire APU lineup from mobile to desktop to server contains the Cortex-A5 and TrustZone functionality.
Having covered the technology, let’s also quickly discuss why AMD is pursuing this move. As AMD is pitching this it’s not just closing a feature gap but also about what it enables. A big focus of this of course is on trusted computing in the classical sense, meaning DRM for consumer applications and on platform lockdown and auditing for business IT purposes. But as we’ve seen Intel do with their acquisition of McAfee some years back, there’s also a strong focus on securing systems from malware in the form of new anti-virus technologies and in newer applications such as mobile payments. Even cloud services get a mention in here, since TrustZone can be used to make sure malware isn’t watching in on a session from the client.
It’s worth noting that AMD also has a bit of self-interest in here. AMD’s Chief Information Officer Mike Wolfe is spearheading this announcement with a focus on how AMD intends to use this technology internally. AMD recently implemented a Bring Your Own Device (BYOD) policy for employees to let them use their own computers at work. BYOD is popular with employees because it allows them to use the device they like the most, but it’s a potential headache for IT since it means many different devices that need to be supported and secured. As a result only a select number of generally high-end devices are allowed in AMD’s BYOD environment because most low-end x86 devices lack hardware security platform technology. By implementing this in their entire range of APUs, AMD expects to be self-serving here by expanding the range of devices they can support. At the same time AMD and Wolfe expect other companies to adopt BYOD too, in which case this will help to quickly set up AMD to serve a potentially large market.
Wrapping things up, we would be remiss to ignore the elephant in the room, which of course is the inclusion of an ARM core in the first place. A lot of speculation has been going on that AMD is considering adopting the ARM architecture on a broader basis – particularly if HSA takes off and makes the underlying architecture less important – and this certainly is going to fuel more of that. The Cortex-A5 in AMD’s future APUs will be a fully functional ARM processor and in theory it is possible to run full ARM applications on the processor (OS differences not withstanding), though at this point in time AMD hasn’t released the full details on how accessing the ARM processor will work. Even if AMD just intends to use ARM for TrustZone today, this opens the door to comprehensive native ARM code execution in the future if AMD wanted to go that way; but at the same time this could end up being as far as AMD ever goes.
In any case we aren’t expecting AMD to go into any more detail about this announcement here at AFDS, but there are still two days of keynotes to go. Otherwise we’d expect AMD to discuss this in greater detail once they’re ready to unveil more details about their 2013 APUs. So until then stay tuned.










36 Comments
View All Comments
Ben90 - Wednesday, June 13, 2012 - link
Pardon my noobness, but I just don't understand the concepts of why this is necessary.Yuriman - Wednesday, June 13, 2012 - link
Taken from arm.com:"TrustZone technology, tightly integrated tightly into Cortex™-A processors, extends throughout the system via the AMBA® AXI™ bus and specific TrustZone System IP blocks. This system approach means that it is possible to secure peripherals such as secure memory, crypto blocks, keyboard and screen to ensure they can be protected from software attack."
In part, AMD is embarrassed that their employees can only bring Intel processors onto their secure work network due to lack of hardware security on AMD's own chips. Hardware level security is the future.
ExarKun333 - Wednesday, June 13, 2012 - link
LOL, yeah they should be a little embarrassed that their own workers cannot bring AMD CPUs into work. :)JKflipflop98 - Wednesday, June 13, 2012 - link
That's funny because Intel still uses Pentium 4's and 1st gen Core 2's internally.Beleaguered - Wednesday, June 13, 2012 - link
Which site and business group runs Pentium 4 laptops? I don't think I've run across anyone at Intel that runs a P4. I have one of the older series for design engineers, and it's a T9400 which is Core2 and still supports TXT. Of course, I'm at the very end of my model's life and moving to SNB within the next month or two.actionjksn - Wednesday, June 20, 2012 - link
How much do you want for the T9400 Processor and is it compatible with a laptop that has a T7300?microlithx - Wednesday, June 13, 2012 - link
DRM, mainly. TrustZone is what Apple and all the Android vendors use to lock down their bootloaders.Netflix requires such locks to appease the MPAA.
taltamir - Wednesday, June 13, 2012 - link
Trusted computing is the holy grail of DRM.The name comes from a CIA in joke, you can only trust a system you compromised and whose user has less control then you do.
It includes hardware chips that verify the hash of software before it is allowed to run. Making it impossible to get a virus. It also makes it impossible to run open source software and it allows remote censorship.
They can decide for example that a certain document needs to go, they send a kill signal and any trusted computing computer out there deletes all copies of said document without the user consent.
taltamir - Wednesday, June 13, 2012 - link
It should be noted that to leverage it in such a manner it needs to be standard everywhere. The hardware makers already put it everywhere.But the problem is laws, which is why there are ongoing attempts to make it legally required (just like for a time HDCP was mandated by law). So far they have failed to do so in the USA. And have yet to mandate big brother.
Jaybus - Thursday, June 14, 2012 - link
It is really quite annoying and downright frightening. An implementation for consumer protection is one thing. For example, modern cars have an electronic ignition key that prevents thieves from making a plain mechanical key and driving off with it. But the key and car, once paired, make a standalone system. Ford can't remotely revoke the key if they decide that you are not driving the car in compliance with an "end user license". Sound crazy? Well, the car and key combination is a form of TPM. It is certainly possible from a technology standpoint for the car to phone home and validate the key.This whole DRM / TPM thing is subverting the very concept of ownership. What does it mean these days to own something? Do you really own something if someone else can control whether or not you may use it? If this is the future, then the future is not unlike the "company store" concept from the 19th century.