Western Digital My Cloud EX2 2-bay NAS Review
by Ganesh T S on March 4, 2014 11:00 AM EST- Posted in
- NAS
- Western Digital
- RAID
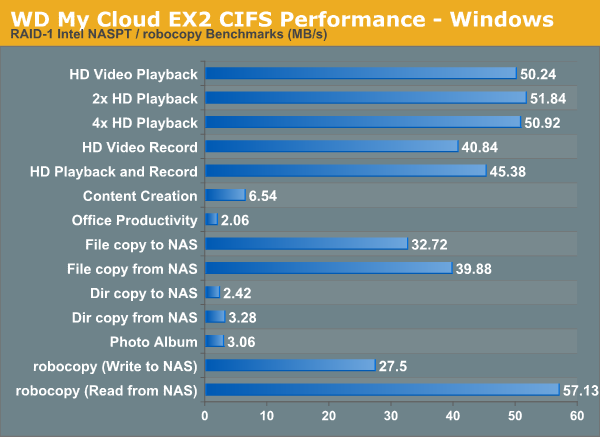
Single Client Performance - CIFS and iSCSI on Windows
The single client CIFS performance of the WD My Cloud EX2 was evaluated on the Windows platforms using Intel NASPT and our standard robocopy benchmark. This was run from one of the virtual machines in our NAS testbed. All data for the robocopy benchmark on the client side was put in a RAM disk (created using OSFMount) to ensure that the client's storage system shortcomings wouldn't affect the benchmark results.
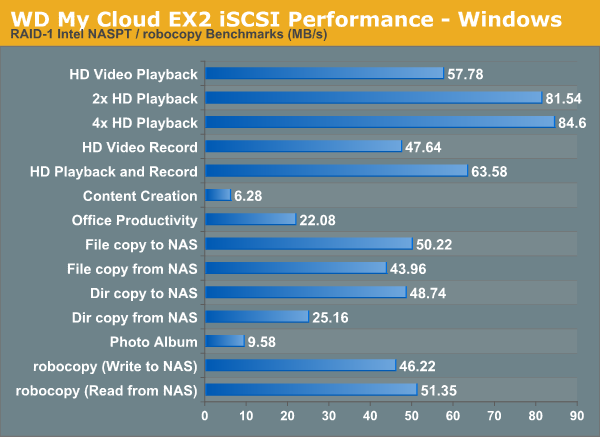
We created a 250 GB iSCSI target and mapped it on the Windows VM. The same benchmarks were run and the results are presented below.
Encryption Support Evaluation:
Consumers looking for encryption capabilities can opt to encrypt a iSCSI share with TrueCrypt or some in-built encryption mechanism in the client OS. However, if requirements dictate that the data must be shared across multiple users / computers, relying on encryption in the NAS is the best way to move forward. Most NAS vendors use the industry-standard 256-bit AES encryption algorithm. One approach is to encrypt only a particular shared folder while the other approach is to encrypt the full volume. Some NAS vendors have support for both approaches in their firmware, but Western Digital only opts for the latter.
On the hardware side, encryption support can be in the form of specialized hardware blocks in the SoC (common in ARM / PowerPC based NAS units). The ARMADA 370 has a 1 Gbps security engine which should accelerate AES operations, but the benchmark numbers below don't point to the utilization of any available hardware acceleration. We enabled encryption on a volume and created a CIFS share to repeat our Intel NASPT / robocopy benchmarks. The results are presented in the graph below (with the unencrypted volume numbers for comparison purposes).
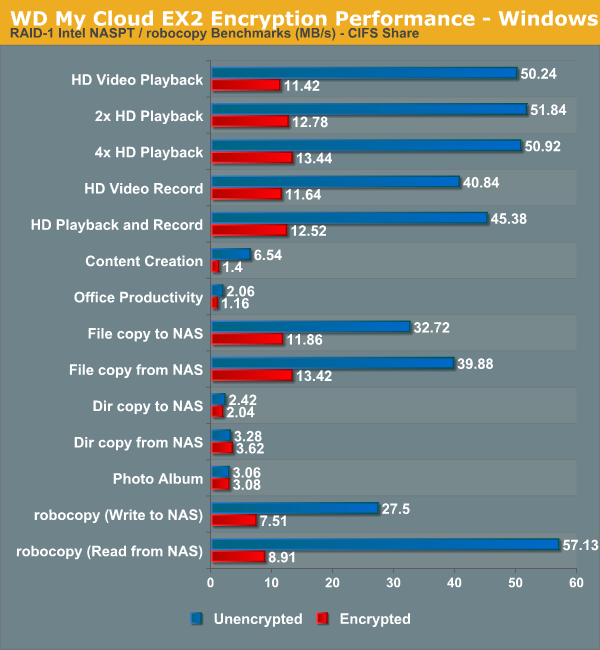
Encryption carries a very big performance penalty (about 5x slower, which is much more than what we saw for the EX4). It looks like there is some scope for improvement in this aspect, particularly if the current firmware is not taking advantage of the security engine in the SoC.










20 Comments
View All Comments
lours - Tuesday, March 4, 2014 - link
What is the default setup for the models that come with drives? What capacity are the drives?hlmcompany - Tuesday, March 4, 2014 - link
As a whole, the unit comes in capacities of 0, 4, 6, and 8 TB. For the units that come with drives, they are the WD Red Drives, such as WD20EFRX, which are slower performing than the 7,200 rpm WD RE4 drives used in this review.ganeshts - Tuesday, March 4, 2014 - link
Configurations with disks are ready to operate out of the box in RAID-1 configuration. So, a 4 TB model, say, will have 2 TB of usable space.As hlmcompany mentions, the WD Red drives are used.
chubbypanda - Tuesday, March 4, 2014 - link
Ganesh,Annoyingly enough, some WD previous models (My Book Studio II) would work only with WD Green drives. Looking at WD's list for EX2, situation is better in this case:
http://www.wdc.com/en/products/products.aspx?id=11...
Oyster - Tuesday, March 4, 2014 - link
This review (including some of the other NAS reviews) seems lacking. What's the point of just showing the read/write numbers without giving us the benchmarks. Like why not show us the comparison to Synology and QNAP 2-bay NAS devices? I'd be more informative to see the performance of things like VM images running off these devices as well. I hope this feedback is accounted for in the future reviews.hlmcompany - Tuesday, March 4, 2014 - link
Agreed. There might even be some relevancy to comparing the My Cloud EX2 with the previous generation model sold as the My Book Live.ganeshts - Tuesday, March 4, 2014 - link
We have already taken care of that aspect in the multi-client tests. Each graph has a drop-down menu under it that allows readers to view the results from the evaluation of similar NAS units. For example, this review lists other 2-bay NAS units that we have evaluated in a similar manner before. The ioSafe N2 presented as a comparison in this review is the Synology DS213. Unfortunately, we haven't evaluated any 2-bay QNAP units.We also have NASPT single-client results for more NAS units. Currently working on a way to integrate a comparison with a drop-down similar to what we have done for the multi-client tests.
As for VM images, can you clarify the exact use-case? I was under the impression that users mount iSCSI volumes on VMs, and we already present iSCSI performance numbers. (at least, that is what I do with some of my VMs).
romrunning - Tuesday, March 4, 2014 - link
To clarify, the comparisons with other 2-bay NAS are only on the "Multi-Client Performance - CIFS" page. It would have been helpful to have them on the other pages with performance graphs, like the Single-client Windows page. That would make it much easier to compare the different models/vendors.Oyster - Tuesday, March 4, 2014 - link
Well, mounting the iSCSI volumes is good, but what I meant was to show us the actual comparisons of VM images running from different devices. So a use case would be to do a big Visual Studio compile on a VM over iSCSI on devices from different vendors. All these vendors claim virtualization compliance, so it'd be nice to put numbers against such claims. Data could include network throughput and CPU/RAM consumption, for e.g. This would also help us understand how good some of the Marvell processors are against Atom/x86. As it stands now, the graphs are too confusing...Also, as others have pointed out, it's a bit tedious to go clicking through every device from the dropdown and not at all intuitive. If I want to look at HD video playback throughput, I should be able to just look at the line graphs of the different vendors in one chart. Kind of like the video card comparison.
creed3020 - Tuesday, March 4, 2014 - link
I also have to agree that a comparison to other reviewed devices is lacking. This could be in the form of updates to the charts so that they show different units e.g. Video Cards FPS benchmarks, or done verbally within the conclusion or it's own section doing a breakdown of each test.These devices are not in Bench so we cannot compare the data there either.