ioSafe N2: A Disaster-Resistant Synology DS213
by Ganesh T S on March 4, 2013 12:00 PM ESTPerformance Benchmarks - Single Client
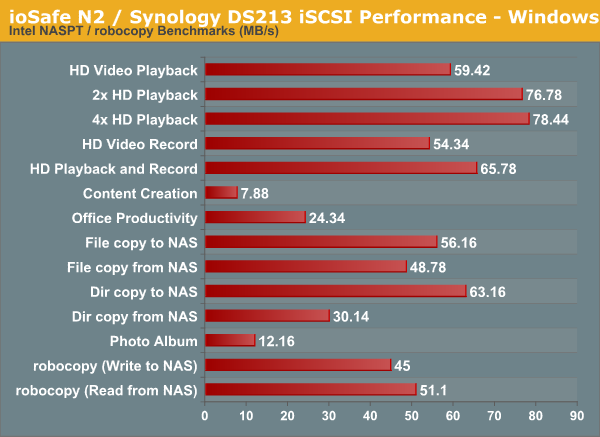
Benchmarks were run under both Linux and Windows for evaluating performance under single client scenarios. Intel NASPT was used under Windows and IOMeter was used under Linux.
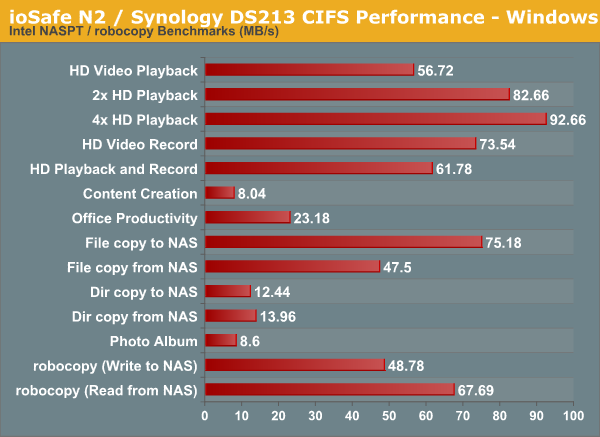
For iSCSI performance evaluation, a 250 GB target was set up and mapped on the benchmarking machine.
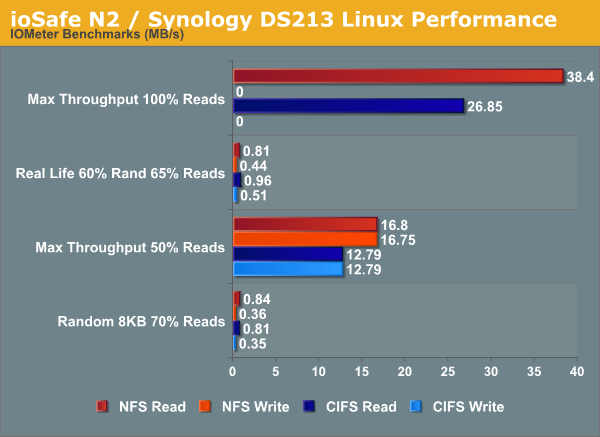
A CentOS 6.2 virtual machine was used to evaluate NFS and CIFS performance of the ioSafe N2 when accessed from a Linux client. In order to standardize the testing across multiple NAS units, the following parameters were used to mount the NFS and Samba shares:
mount -t nfs NAS_IP:/PATH_TO_NFS_SHARE /PATH_TO_LOCAL_MOUNT_FOLDER -o async,hard,proto=tcp,noac
mount -t cifs //NAS_IP/PATH_TO_SMB_SHARE /PATH_TO_LOCAL_MOUNT_FOLDER -o directio
Note that we have not tried to optimize NFS performance for the NAS. In order to keep things as uniform as possible, we will just look at comparative performance on the basis of the default mounting options combined with the above (which are set to avoid caching effects on the client side). The scripts available here were run on IOMeter. The graph below presents the various results.










26 Comments
View All Comments
zepi - Monday, March 4, 2013 - link
"Even the physical theft protection aspect can be easily handled with the Kensington lock feature."Considering that 12mm (half an inch) steel-cables / U-locks are unable to prevent bicycle theft, I really doubt that anything a Kensington lock could be attached to would prevent anyone from stealing the thing.
Cstefan - Monday, March 4, 2013 - link
I've enjoyed demonstrating the worthlessness of these to company bigwigs that about 1 minute with medium duty snips is all it takes.ganeshts - Monday, March 4, 2013 - link
Point noted, but it does act as a first-level deterrent. The unit is really heavy too, and combining these two factors, I think a casual break-in will probably result in the N2 being left alone.Penti - Monday, March 4, 2013 - link
It's actually more a insurance thing from what I gather. As they wouldn't cover something left unattended. It has nothing to do with actual physical security, especially not for server side equipment. Companies tend to lock the computers in computer security cabinets itself in a locked room at the end of the day if they care or has any policy regarding security/theft.robb.moore - Tuesday, March 5, 2013 - link
Penti-You're right. Most companies that care about physical theft security have their equipment in a closet or locked room. That being said, we're releasing a floor mount locking kit for the N2 which allows the N2 to be bolted to the floor or wall. It'll also allow the block all access to all ports and screws (front and back) with a steel panel that can be padlocked into place.
In regards to physical security, it's an issue as with anything - you get what you pay for. Class 3 Bank Vaults cost more than an Ace Hardware padlocks. With ioSafe, we are constantly thinking about what makes the most sense from a cost, weight and user's perspective.
We consider the N2 a building block to help with businesses dealing with vulnerable data. Multiple N2's hidden and synchronizing on the LAN might be a good solution for some businesses. Using a combination of N2's, traditional cloud and offsite vaulting also might work for some businesses. No one solution works for everyone.
Great discussion.
Thanks!
Robb Moore
CEO
ioSafe
sphigel - Tuesday, March 5, 2013 - link
The odds of a bike thief having a bolt cutter are pretty good. The odds of a home burglar having a bolt cutter are significantly less I would think. Without a bolt cutter these Kensington locks would be a pretty strong deterrent.BrokenCrayons - Tuesday, March 5, 2013 - link
I've had to remove Kensington-style locks at my office from laptops when combinations are forgotten or keys are lost. All that's required is a folding multitool (Gerber, Leatherman, etc.) and couple of minutes to gnaw at the cable after using the knife or saw blade to slice away a bit of the plastic jacket (which isn't necessary depending on cable thickness. Of course, taking out the hard drive and protecting the laptop from metal fragments when cutting down the actual lock to take it apart is a little bit more of a pain, but that can happen at someone's leisure after a theft has happened.secretmanofagent - Tuesday, March 5, 2013 - link
That, and I'm pretty sure they're just going to yank it really hard if they don't want to wait.bbomb - Monday, March 4, 2013 - link
No physical testing of the waterproofness or fireproofness?Samus - Tuesday, March 5, 2013 - link
There are some pretty ridiculous videos on YouTube, one involving it being driven over by a bulldozer.