AnandTech Year in Review 2018: CPUs
by Ian Cutress on December 27, 2018 3:30 PM EST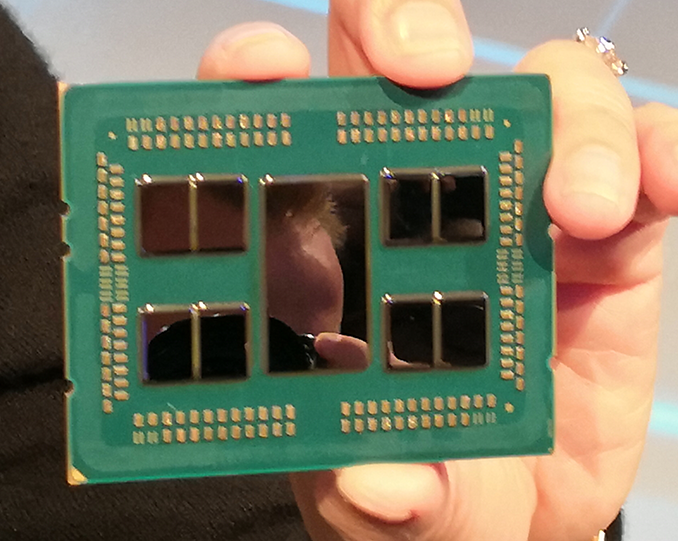
When Ryan initially asked me to write a roundup of the year’s news on CPUs, I laughed. There has been a lot going on this year, from processor releases and reviews, to security issues, to discussions about the next few years of computing. However a couple of weeks ago I wrote a script to pull every AnandTech article out of our archive to filter into my own database for analysis. It turns out that the AT staff between us have written just shy of 200 news articles and longer format reviews about CPUs this year, and here are the highlights.
When discussing CPUs, at least the desktop market, our attention focuses to two companies in particular: Intel and AMD.
January: Security and CES
The start of the year typically begins with the big CES trade show in Las Vegas, but before we event got to that point, news broke about two new classifications of vulnerabilities affecting most modern processors: Spectre and Meltdown. This was significant as these two names signified a new family of microarchitectural vulnerabilities derived from the base design of modern processors, exploiting some of the tricks used for how we get a lot of speedup in common day-to-day tasks. The news broke about a week earlier than the companies intended (part of the term responsible disclosure), but the big players having around six month’s notice to put forward fixes after Google’s Project Zero first discovered them in 2017. These vulnerabilities were a common thread through 2018 (and still are today), as companies put forward a mix of software and firmware fixes for hardware in the wild, built security assurance teams, and put research towards hardware fixes for future products. Essentially every high-performance processor ever made – Intel, AMD, ARM, and POWER – is thought to be vulnerable at some level, and every major company made official statements on the issue. Software and firmware fixes for several generations of processors came out through 2018, and new products that block ‘some’ of these attacks came out in the latter stage of 2018, although 2019 is where it gets more serious. Some of these fixes cause performance regression in certain tasks, mostly enterprise based, however this is a topic that will also be at the forefront of every 2019-2020 CPU launch.
Not to be outdone by security news, the CES trade show was one of our busiest ever. AMD kicked off proceedings with a full day of discussions, keynotes, and disclosures. The key to AMD’s presentation is that the new Zen microarchitecture products, Ryzen and EPYC, were paving the way for the future. In the presentations, AMD presented roadmaps for product launches in 2018, including new APUs, a new range of desktop processors on 12nm with Zen+ updates, second generation Threadripper on the high end, and a push towards 7nm Vega GPUs at the end of the year. This was a very well put together presentation from AMD, showing that they have roadmaps and they are willing to commit. On top of this, AMD reiterated its long term roadmap on CPU and GPU technologies, going through 2020.
One key highlight here was our interview with AMD’s CEO, Dr. Lisa Su, on how AMD is set to approach its new era.
Intel had its usual keynote at CES, hosted by now former CEO Brian Krzanich, which addressed the security issues briefly, spoke mostly about drones and connecting people, but made no mention of the company’s progress on its next generation process technology at 10nm. Instead, the company mentioned 10nm very briefly at the end of a small 9 minute presentation at the Intel booth the next morning, at 8am, through Gregory Bryant, the SVP of the Client Computing Group. The news wasn’t that great: Intel confirmed it had shipped 10nm in 2017 for revenue. It was literally that short of a sentence. No word on how the technology was progressing, or any future timelines.
There was some upside for Intel in January however. The company launched its best performing integrated graphics solution ever: the Core with Radeon RX Vega Graphics set of SoCs. These processors took quad-core mobile chips and paired them with a custom Polaris graphics solution from AMD all on the same processor package. The graphics chip was connected with Intel’s EMIB technology to a stack of HBM2 memory, keeping the package small. The offerings ranged from 65W to 100W TDP, and the goal here was to provide something just below discrete graphics solutions in a thin and light form factor. We saw the HP Spectre x360 and Dell XPS 15 both updated with these options, as well as a Hades Canyon NUC, a Chuwi HiGame mini-PC, and a Dell Precision device later in the year.
February: Visiting GlobalFoundries
Transitioning from January to February is usually a slow time in the industry as Chinese New Year sets in. Depending on the company, this can be anything from a one week break to a three week break, so we don’t tend to see many product launches at the end of January/beginning of February unless the factories have enough stock, or the fabs chain doesn’t involve China.
Intel kicked off the month with a reactionary measure to the Spectre and Meltdown issues by formally announcing the creation of the Product Assurance and Security Group (which had technically been reported in January, but wasn’t formal until this point). The strategic goals of the group were unclear, except that the group will coalesce Intel’s ‘cross company efforts to continuously improve product security’.
In the first week, Intel also launched its Xeon D-2100 platform, placing it in a spot above its previous Xeon D-1500 line-up. These processors were different to the older ones because instead of using mainstream Core cores, they were essentially the same as the Xeon Scalable line of processors, albeit with lower frequency, lower TDP, but focused on integrated networking and QuickAssist features. Parts are in the market up to 18 cores.

A 'bunny suit' for inside the Fab. Unfortunately, no pictures allowed inside.
Also in that early part of February, Nate and I visited GlobalFoundries Fab 8 in Malta, New York. At this time, GF was the talk of the town, having successfully executed AMD’s strategy with Ryzen and EPYC, and were looking forward to both 7nm and EUV products. Having a look inside a modern fab is a rare thing indeed, and it opened our eyes to the fact that these are more than just black box factories and require leading edge technology and setups to execute as required. We also interviewed CTO Gary Patton about the fab and the future of GF through 2018.
On AMD’s side of the fence, the company launched its first desktop APUs, combining Zen cores and Vega graphics in a desktop form factor. The Ryzen 5 2400G and the Ryzen 3 2200G both offered compelling features: reasonable 720p gaming with four cores starting at $100. Along with the processors came a series of stock coolers that put everything else to shame. AMD also launched its EPYC embedded platform, offering a range of Ryzen-like products for integrated systems.
March: Security Again
The end of Q1 was our quietest month of the year in terms of absolute CPU news, although a couple of big elements came to the fore. Aside from our analysis into Ryzen Threadripper coolers with large base plates, such as the Noctua NH-U14S TR4-SP3, Intel also discontinued the ‘n-1’ family of Poulson Itanium processors, putting the penultimate nail into that family of products.
If the security issues of Spectre and Meltdown were not enough, some other security issues came to light. A previously unknown security company, CTS-Labs, announced it had found several vulnerabilities within ASMedia chipsets and AMD’s Secure Processor. We covered the issues in detail, however there were many questions about how this announcement came about: the security firm offered the companies no form of responsible disclosure (they even said it was a bad idea), no strict details on the vulnerabilities, produced a website in advance to promote the issues, hired a PR firm to handle it with professionally rendered videos about the issues, and some supposedly unrelated financial firms were ready with multi-page documents stating the issues meant that AMD was worth zero. In our interview with the company, it was clear that there were technical miscommunications, and when we asked about the backers for this project, the call was abruptly ended. I recorded a two-hour podcast/video on the issue with TechTeamGB, which is worth watching.
AMD, after a week to analyse the findings, subsequently released a statement on the matter. The truth is, most of the exploits were secondary vulnerabilities – they required elevated permissions to begin with. However AMD confirmed that fixes would quickly be in place. The security company has not been heard from since, and the website they produced to promote the issues no longer exists.













42 Comments
View All Comments
damonlynch - Thursday, December 27, 2018 - link
The lowpoints involving CTS-Labs and Krzanich demonstrate the enduring importance treating others with respect. In these instances selfishness and dishonesty were not rewarded. Moreover, one has to wonder what the medium to long-term cost will be of Krzanich's slashing Intel's research expenditures. That has to hurt.Oxford Guy - Friday, December 28, 2018 - link
Respect, like when Google hacked iOS and Safari to install spyware payloads (evercookies)?Or, when it helps with metadata-using algorithms to target US citizens for drone elimination?
Or, when it lied to its own people over China's Dragonfly? Shall I continue?
Reality is that when someone stomps their feet and points fingers when anyone, whether it's a journalist or a self-described security company, exposes flaws in products that have been sold in the market — the blame for those flaws rests solely on the company that created them and put them into the marketplace. Do not shoot the messenger, no matter how much of the guilty company's stock you own.
Google isn't your friend either. No corporation is. They're all out for one thing and one thing only: profit for their people.
Wild-eyed cries, demands for censorship, place the world at greater risk than transparency does. People are owed the knowledge of defects in their products, immediately. It should always be assumed that bad actors have the information during these blackout periods. CTS did the right thing by refusing to have a long one so the guilty party (AMD) could diminish its accountability with PR machinations.
Public outrage is maximized when knowledge is given to them immediately. That's why coverups last for such a long time. We get to find out about the bad deeds decades later, like how the government settled with the family of an intelligence worker who was apparently pushed out of a tall building to keep him from blowing the whistle. Muzzling the so-called free press is not the way to go but there is so much clamor in the tech community for exactly that. The ideological difference between us Westerners and the Chinese is what, exactly?
Respect is earned, not given. Companies that sell defective products have the responsibility to find the problems, make the knowledge public immediately, and fix the problems with maximum haste. They don't have the responsibility to lazily wait for PR-friendly media blackouts arbitrarily chosen by random third parties (particularly those intent on devouring the Internet like Google) expire, after those random unelected third parties find them.
Lord of the Bored - Friday, December 28, 2018 - link
Man, I thought the CTS shills died when their blatant stock-shorting scheme collapsed on its face.tamalero - Saturday, December 29, 2018 - link
They probably have a contract for botters that act like shills to defend the brand. It happens a lot lately.Oxford Guy - Sunday, December 30, 2018 - link
The same ad hominem can be applied to posts like yours. Post a rebuttal and refrain from posting spam.Oxford Guy - Sunday, December 30, 2018 - link
No rebuttal, just an ad hominem. Par for the course.kd_ - Friday, December 28, 2018 - link
LolOxford Guy - Sunday, December 30, 2018 - link
The idea of a free press is humorous in some circles.The idea that consumers should be informed when the products they have been sold are defective is humorous in some circles.
The idea that companies shouldn't be able to collude with unelected third parties to muzzle the tech press, so that PR damage control campaigns can minimize accountability is humorous in some circles.
If any of you truly believe that it's a good thing to have press censorship to protect the reputations and stock prices of companies from ordinary people (rather than insiders) that sell defective goods, then I suggest codifying that with an elected and accountable body rather than blithely enabling for-profit corporations, which do not have a mandate to work in the public interest, to control the narrative and the flow of information with whatever arbitrary processes they dream up to help with their quest for profit and dominance. This means things like standardization in procedures (such as the apparently very beloved first-amendment-quashing blackout periods), standards that are voted on and vetted by a larger community than various corporations' executives.
(Oh, look, it's a bot! It's not the person posting "Lol" or the brainless ad hominem one-two sentence troll posts that so many in the tech community think are impressive enough to masquerade as a rebuttal.)
gteichrow - Thursday, January 24, 2019 - link
Well said.Flunk - Saturday, December 29, 2018 - link
Good luck with the word-salad of irrelevant whataboutism. OP didn't say a word about Google.