ioSafe 1513+ Review: A Disaster-Resistant Synology DS1513+
by Ganesh T S on August 13, 2014 7:30 AM EST- Posted in
- NAS
- Storage
- Synology
- Enterprise
- ioSafe
Single Client Performance - CIFS & iSCSI On Windows
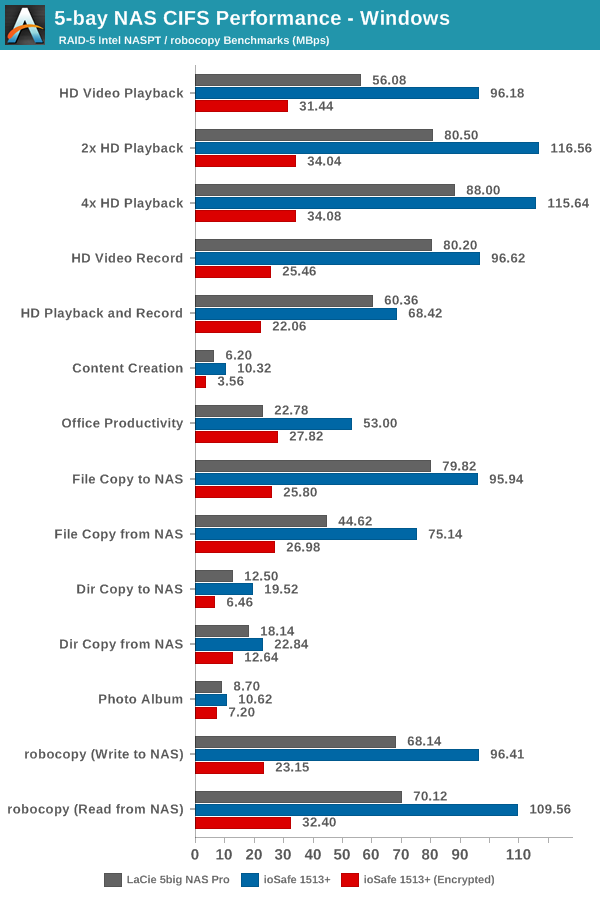
The single client CIFS and iSCSI performance of the ioSafe 1513+ was evaluated on the Windows platforms using Intel NASPT and our standard robocopy benchmark. This was run from one of the virtual machines in our NAS testbed. All data for the robocopy benchmark on the client side was put in a RAM disk (created using OSFMount) to ensure that the client's storage system shortcomings wouldn't affect the benchmark results. It must be noted that all the shares / iSCSI LUNs are created in a RAID-5 volume.
The market doesn't have too many 5-bay NAS units. In fact, the only other 5-bay NAS unit that we have evaluated before is the LaCie 5big NAS Pro from early 2013. That unit was also based on the Intel Atom D2701, but carried only two GbE links instead of the four in the ioSafe 1513+. In terms of encryption support, vendors have two approaches - encrypt a particular shared folder or encrypt the full volume. Synology only supports folder-level encryption in DSM. The graph below shows the single client CIFS performance for standard as well as encrypted shares on Windows.
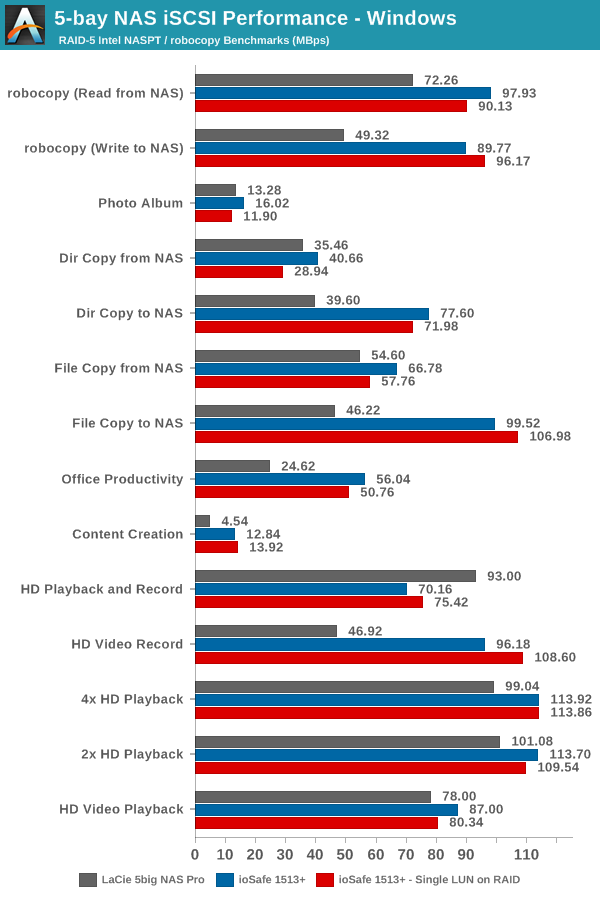
We created a 250 GB iSCSI target and mapped it on to a Windows VM in our testbed. The same NASPT benchmarks were run and the results are presented below. Note that we also present numbers for the 'Single LUN on RAID' mode which is supposed to provide the best access performance. It does indeed perform better with write workloads, but loses out on read workloads to the standard file-based LUNs.










43 Comments
View All Comments
ddriver - Saturday, August 16, 2014 - link
Thanks for the input. BTW, where I come from, "cellar" does not imply "basement" - our cellars are usually on floor levels, tiny room, around 1 m^2 for general storage purposes, no water mains no nothing. Closer to what you may call "pantry" in the US. Cultural differences... me'h. Nothing to burn and nothing to flood in there. Plus noise in the cellar bothers nobody.Never failed a demo - which exactly proves the point I make earlier about being careful with controlled fires. That would create the illusion your products are flawless and someone's gonna buy one expecting it to survive his fancy wooden and lacquer soaked cottage burning to the ground which I am willing to bet it will not. You should really draw the line between "office fire accidents" and "fire disasters" just for the sake of being more realistic and not deceiving consumers, deliberately or not. People are impressed by big numbers, and could easily be impressed by the 1700 F number, absent the realization most flammable materials burn at significantly higher temperatures. Every engineer knows - there is no such thing as a flawless product, the fact you never had a failed demo only goes to show you never really pushed your products. With those zero failed demos you will very easily give consumers the wrong idea and unrealistic expectations, especially ones who are not educated on the subject. You SHOULD fail a few demos, because it will be beneficial for people to know what your products CAN'T HANDLE. A few failures in extreme cases will not degrade consumer trust as your PR folks might be prone to believing, it will actually make you look more honest and therefore more trustworthy.
ddriver - Saturday, August 16, 2014 - link
I mean better you cross that line with a test unit than some outraged consumer going viral over the internet how your product failed and he lost his life work ;)robb.moore - Monday, August 18, 2014 - link
Hi ddriver-As mentioned, our fireproof tech relies on proven methods that are over 100 years old. Appreciate the heated skepticism though. As an engineer myself, I agree that no product is flawless and everything (including our own products) have their limits. I take back the "never failed a demo" comment. We did some gun demos with shotguns (passed) - got a bunch of flack for ONLY using shotguns so we redid the demo with fully auto AR-15's - blew holes completely through the product and of course failed...sometimes. Fun demo though.
-Robb
Phil Stephen - Monday, August 18, 2014 - link
ddriver: I'm a firefighter and can confirm that, based on the specs, these units would indeed withstand a typical structure fire.zlobster - Sunday, August 17, 2014 - link
Dear Mr. Moore,I'm really glad that you actually follow up with the public opinion.
I'll try to use the opportunity and use it to ask you whether you are planning to build a unit with non-Intel CPU, rather with AMD/ARM/Marvell/etc.? A unit that can handle the latest industry standards for on-the-fly encryption without sacrificing the performance even a bit?
Also, besides the physical integrity and resiliency tests that you are conducting, do you do similar penetration-testing for data integrity? I mean, with well-known independent hacker/pen-testing communities? With all the fuzz around govt. agencies putting backdoors virtually everywhere, it's of extreme importance for the piece of mind of extreme paranoics (like me), to know how hack-proof your devices are.
Regards,
Zlob
robb.moore - Monday, August 18, 2014 - link
Hi Zlop-We're constantly working on new products. The 1513+ does use an Intel chip but our other NAS (2 bay), ioSafe 214 uses a Marvell chip. We realize that encryption can be important in many situations and we're always interested in balancing features, cost and speed for our products. Can't make direct comments though on what we have in the pipeline except stay tuned! :)
In regards to "hack-proof", the most "hack-proof" systems (aka CIA, etc.) don't exist on the internet at all. They're fully contained offline in secured facilities. In fact, ioSafe systems are used in situations like this where offsite backup (online or physical relocation) is not allowed or impractical but the end user still wants a disaster plan.
Obviously, there's a balance between security, accessibility, cost and speed. If you put an ioSafe system online, no firewall, never update OS/firmware, all ports open with standard admin passwords - expect mayhem. If you put an ioSafe system in a bank vault, offline and turned off it's obviously pretty secure but inaccessible - not very useful. Security can be complicated. Striking the right balance is different for every situation. Our NAS systems are based on the Synology platform which in turn is a custom Linux kernel so it's as safe as you make it generally (like all connected systems) and is susceptible to hackers if setup incorrectly. We're very happy to help you with configuring your device if you have any questions at all about the tradeoffs.
Ultimately though its under your control. You're in charge of opening or closing doors.
Robb Moore, CEO
ioSafe Inc.
PEJUman - Saturday, August 16, 2014 - link
I second that, for this price... I really want to know it it would last the rated time under fire. Should try it under propane {bbq tank 2300+ C} and and Nat. Gas/wood based flame {1900+ C} To simulate household/industry gas line.bsd228 - Thursday, August 14, 2014 - link
Well for the $1000 extra, one could buy a 30"x72" inch gun safe that can also be used to store the regular Synology (or a DIY NAS) plus guns, camera gear, and any other valuables. Harder to steal as well- they weight 500-1000lbs.DanNeely - Thursday, August 14, 2014 - link
Maybe; but good luck using the NAS with the door shut...smorebuds - Thursday, August 14, 2014 - link
l0l