Thunderbolt on Windows Part 2: Intel's DZ77RE-K75 & ASUS' P8Z77-V Premium
by Anand Lal Shimpi on June 3, 2012 2:08 AM EST- Posted in
- Motherboards
- CPUs
- Intel
- Asus
- Thunderbolt
- Ivy Bridge
- Chipsets
Hot Plug & Promise Pegasus, Now Supported Under Windows
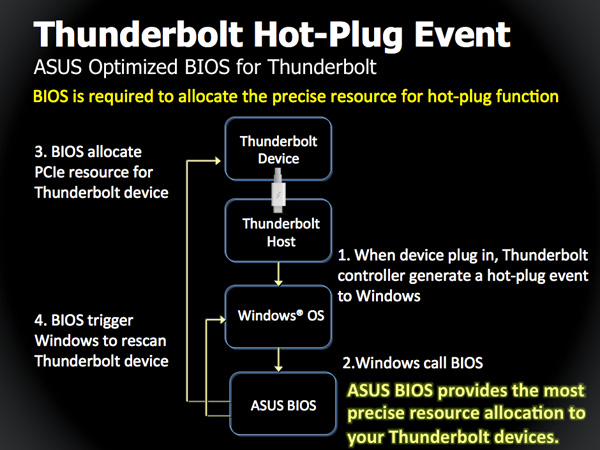
For the past year, hot plug of Thunderbolt devices hasn't been supported under Windows—even on a Mac running Boot Camp. Any Thunderbolt device had to be present at POST for it to appear under Windows. In order to have a certified motherboard, BIOS/UEFI workarounds have to be present to allow for Thunderbolt hot plugging under Windows.
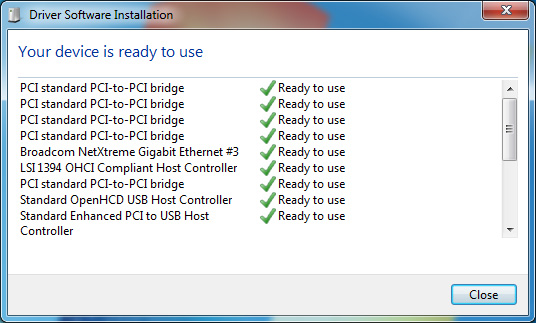
With a certified motherboard and a Windows certified Thunderbolt device, hot plug does work as you'd expect it to.
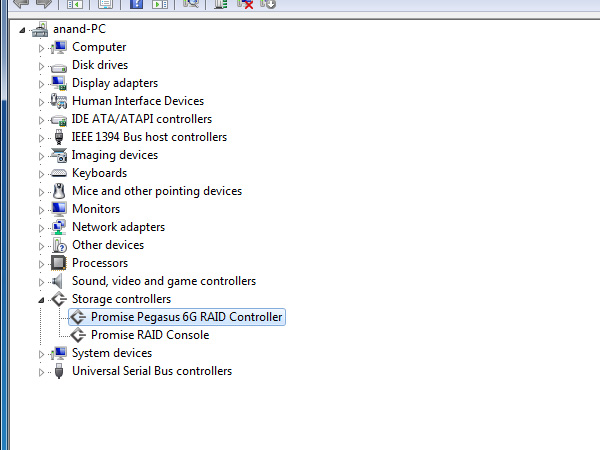
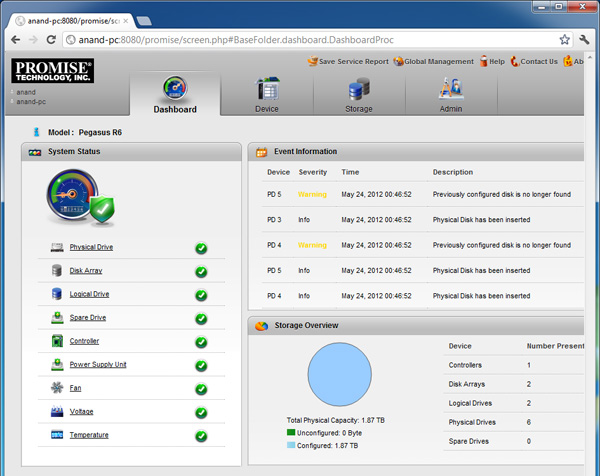
Promise provided us with a beta driver and firmware update that allowed us to use the Pegasus R6 under Windows. Hot plugging worked just fine.
The Promise Pegasus utility under Windows is actually a web based interface, but it provides the same basic functionality as the equivalent OS X application.
What happens if you don't have a certified driver? One of three things can happen. The device will either not work at all, it will compromise stability, or it will work but with some issues. The LaCie Little Big Disk is the perfect example of the last option. I just got a beta certified driver, but prior to receiving it this is what would happen when I plugged it into a running Windows system:
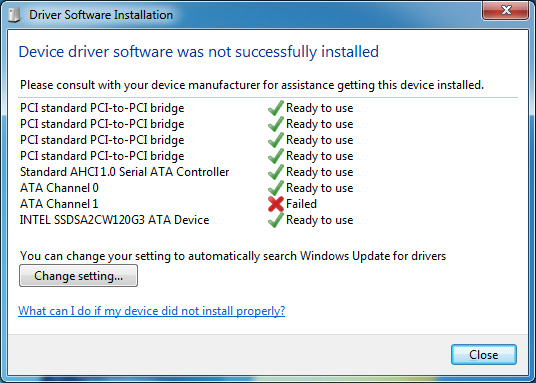
Only one of the two internal SATA channels was detected, meaning only one of the two internal drives was accessible. A reboot fixed this however.
The Elgato Thunderbolt SSD and Seagate's 2.5" GoFlex Thunderbolt adapter both use a different (lower power) SATA controller in order to stay below the 10W limit for a bus powered device (the cable, SATA and pre-Cactus Ridge Thunderbolt controllers combined already eat up around 5W).
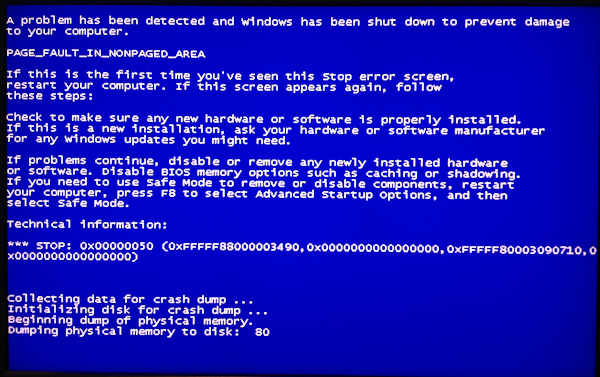
Unfortunately the ASMedia controller in these devices doesn't work well without a certified driver. Simply attaching the Elgato drive to a running Windows PC can cause a BSOD. Neither drive would even show up on either of the motherboards I tested; we'll simply have to wait for a certified driver here.
Apple's Thunderbolt Display works but not without a bunch of caveats. First you'll need access to a Mac to extract the drivers for the integrated components in the display (Firewire 800, GigE, etc.). Audio will work but only if you don't have a discrete GPU plugged into the motherboard. Firewire 800 and GigE both work. The integrated USB hub on the other hand basically doesn't work under Windows. Apple doesn't officially support the Thunderbolt Display under Windows and Intel won't certify it without Apple's support so anyone wanting to use a Thunderbolt display will just have to wait for someone else to release a similar product.
Remember the weird audio frame dropping issue I encountered under OS X with the Pegasus and Thunderbolt Display? I also encounter a similar but less severe version of that under Windows. While writing to the Pegasus and playing music through the Thunderbolt Display's speakers I get dropped audio frames, but unlike under OS X the music continues to play and is mostly recognizable—it just sounds like there's a little bit of static in the background. It's interesting that the problem exists under both OSes, but with slightly different behavior.
















116 Comments
View All Comments
ka_ - Monday, June 4, 2012 - link
The one thing that will keep me away from TB is the major problem that any device can access the DMA of any connected devices essentially removing all security of any system with TB - except if by disabling DMA while using the plug. I have come to notice that Apple have a undocumented method to disable DMA on TB <http://matt.ucc.asn.au/apple/>, though it indicates this method only apply to the Firewire over TB exploit, and it likely is not much time until someone have a better method. But if it is possible do disable DMA/restrict DMA access on the machines, then TB might even eventually get accepted by the security focused audience too?If possible do disable DMA under Windows/Linux how much would this degrade the TB performance?
repoman27 - Monday, June 4, 2012 - link
Disabling DMA for Thunderbolt is akin to disabling DMA for PCIe, i.e. not practical. IOMMU will hopefully provide security for these types of scenarios, but the driver implementation just isn't there yet.Does the fear of DMA attacks prevent you from using PC's with available PCIe slots, ExpressCard or IEEE 1394 ports? Hardware DMA attacks require physical access to the machine or some sort of social engineering ploy. If an attacker has physical access to your machine, they would most likely try many other vectors before resorting to a DMA attack. DMA attacks generally involve custom hardware which is time consuming and expensive to develop. Do you really see someone buying or creating a custom piece of Thunderbolt hardware just to attempt to compromise PCs under your control?
While these types of security vulnerabilities are real, exploitation of them is rather uncommon, and for the foreseeable future, far more likely to come in the form of FireWire or ExpressCard than Thunderbolt.
If someone ships you a shiny new Pegasus R6 with a note saying, "You're the lucky winner!" just sell it on eBay and move on.
ka_ - Monday, June 4, 2012 - link
"While these types of security vulnerabilities are real, exploitation of them is rather uncommon, and for the foreseeable future, far more likely to come in the form of FireWire or ExpressCard than Thunderbolt."Completely wrong - The firewire exploit is possible to do on any TB and the exploit is already in the wild: <http://www.breaknenter.org/2012/02/adventures-with...
Even script kiddies can apparently do this attack against TB and firewire already...
So yes - I would indeed sell the machine coming with this port unless there is a way to prevent DMA access for units connected through the TB port.
I think Asus UX32VD-DB71 or one of the UX31A's which does not have TB, Firewire, ExpressCard or any of the other easily exploitable ports.
repoman27 - Monday, June 4, 2012 - link
Did ya read the article you linked to? Did ya understand any of it? Because I had already done so, and came away with a very different assessment of the severity of the threat in question.The exploit as described is a FireWire DMA attack requiring physical access to the PC along with several bulky hardware devices costing many hundreds of dollars. The pointlessness of this exercise is especially extreme, because at the time it was written, the only PC with Thunderbolt but lacking FireWire was the 2011 MacBook Air.
I don't generally let script kiddies hang out in my house, but I'd probably notice if they left an Apple Thunderbolt Display or a Sonnet Echo ExpressCard/34 Thunderbolt Adapter, ExpressCard FireWire adapter, 2.0 m Apple Thunderbolt cable, FireWire cable and "attack" PC running Linux lying about attached to my MacBook Air. Just sayin'.
ka_ - Monday, June 4, 2012 - link
The article specify "or equivelent" - ebay got a thunderbird to firewire adaptor from USD 4.25And no - you dont need daisy chain except to test some of the more advanced hacks there...
http://www.ebay.com/itm/6-pin-Firewire-to-Thunderb...
repoman27 - Tuesday, June 5, 2012 - link
That's a 6-pin to 8-pin FireWire adapter you moron.I guess if you can fall for eBay listings like that, you need to protect yourself pretty darn well against potential social engineering attacks. Good luck with that.
repoman27 - Tuesday, June 5, 2012 - link
Sorry, I didn't really mean to call you a moron. I wish this site allowed editing of posts.ka_ - Tuesday, June 5, 2012 - link
No problem - I might have been to hasty including the first search result I found for "Thunderbolt to Firewire" converter/adapter. There are others too such as<http://istore.techtools.com.au/index.php?route=pro...
The real point I am trying to make is that you most certainly wont need expensive hubs or daisy chains to perform this attack - any adapter/converter will do.
In fact - Firewire was only used to demonstrate that the problem still persist with Thunderbolt. That particular exploit can be prevented by simply blacklisting Firewire / 1394 devices, however that is only keeping the currently known exploit from happening.
Since Thunderbolt have DMA access on its own, it is only a matter of time before an exploit can be made with no conversion at all!
I know there are USB2/3 to Firewire converters too, which might make USB3 vulnerable to the same exploit even though USB3 in itself does not have DMA access. So all firewire is indeed on my blacklist even though I don't have any firewire ports on my laptop.
jontech - Monday, June 4, 2012 - link
enthusiasts would have been tripping over themselves calling it the second coming.The fact is, Intel can ramp up TB to 100GB in the next couple of years. USB can't keep up.
The footprint is much smaller, mDP vs USB so it's perfect for Notebooks and allows for breakout and dock solutions that include many other technologies
It is here to stay, and the fact that Apple pushed it and has every one of their computers with it means that those companies who have made TB devices have been rewarded with sales.
rs2 - Tuesday, June 5, 2012 - link
You killed my interest in Thunderbolt when you said:"Interfaces like USB are great because you can generally count on anything that physically fits in the port just working. With Thunderbolt on Windows we now have a situation where you can't assume the same."
That is *not* the way to introduce a new connectivity standard. If I can't plug any Thunderbolt device into any Thunderbolt connector and *know* for a fact that it will work without issue, then something is very seriously wrong.