Cinavia DRM: How I Learned to Stop Worrying and Love Blu-ray’s Self-Destruction
by Ganesh T S on March 21, 2012 11:00 AM EST- Posted in
- Home Theater
- Blu-Ray
- DRM
- Cinavia
Content providers mandate the presence of protection schemes at all times when the consumers want to access their wares. For the consumer, this entails:
1. Conditional access
2. Protected transmission
3. Protected distribution
4. Protected storage
Conditional access is applicable to cases where media travels over insecure channels (such as satellite or cable). This is implemented in STBs. Protected transmission is the path to the display device, and it is usually protected by HDCP (over HDMI) or Macrovision in legacy systems. Protected storage is encountered in broadcast content, with its copy flags to allow DVR archiving. Protected distribution is enabled by the DRM mechanism in Blu-rays / DVDs. In Blu-rays, this DRM scheme is called as AACS (Advanced Access Content System). AACS also provides for protected storage through the Managed Copy feature.
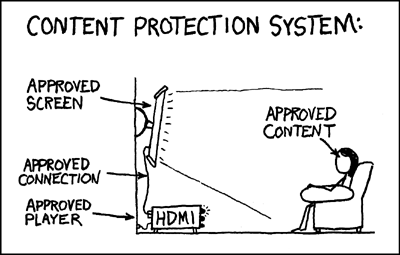
A Popular Webcomic's Take on DRM (c) xkcd
AACS uses 128-bit AES for encryption. Each Blu-ray player / device has a Device Key, while discs come with a Media Key Block (MKB). The shared key generated by using these two (Media Key) is used to decrypt the Title Key, which is then used to decrypt the audio/video data in the disc. AACS also has a revocation mechanism. The MKB in each disc has a Host Revocation List for software players and a Device Revocation List for hardware drives. For PC-based playback to be successful, both the player and the drive must not be on the revocation list.
In practice, key revocation is quite rare because device keys could be shared across an entire lineup, making it hard to pinpoint which particular device was compromised. AACS does provide some sequence keys to identify a particular device as compromised if one has access to multiple pirated copies of different discs from the same drive. In addition to the MKB-Media Key-Title Key combination, PC-based players also have support to generate a Shared Bus Key to encrypt the data inbetween the drive and the software player. This ensures that any snooped data can't be used to get to the original content on the disc. AACS also has a renewal process to prevent attacks similar to those carried out on CSS (with DVDs). The net result is that we are currently at AACS v30.
In addition to AACS, the BDA mandates a BD-ROM mark, which is a physical irregularity on the disc with a 128-bit VolumeID. Blu-ray players will not play back protected content without the VolumeID, as it is essential to the decryption process. Also, the VolumeID can't be generated by consumers (BD-Recorders don't have the capability to burn a VolumeID). The process is tied to the manufacturing facility (which can obtain a license only under strict security considerations). With a counterfeit Blu-ray, it is a simple matter of using the VolumeID to trace the place where the piracy took place.
Note that AACS is based solely on cryptography and, after having been compromised, has the possibility of revoking cryptographic keys as the only means of regaining its effectiveness. So far, this method has failed. This has tempted studios to move over to other forms of DRM such as BD+ and Sony Screen Pass.
It is mandatory for players to implement support for BD+, but not all Blu-rays need to be BD+ enabled. From a player's perspective, a Security Virtual Machine (SVM) needs to be implemented. Blu-rays with BD+ have special content code which are loaded by the SVM and executed during the playback process. The content code has full control over all the components involved in playback. It can alter menus and show on-screen messages if some security breach is detected in the player.
One of the most common BD+ implementations involves storing garbled video on the disc (i.e, after AACS decryption, certain segments of the video are distorted). The content code can implement a fix for the distorted video so that licensed playback is still problem free. For example, in the recently released Contagion Blu-ray, watching the disc with an old version of AnyDVD HD (which performs only AACS decryption, say) would result in heavily distorted video in various scenes. This is because the BD+ code to fix the video wasn't being executed by AnyDVD HD. Unlike AACS, technologies such as BD+ from Irdeto (responsible for the BD+ in the Contagion Blu-ray) and Sony Screen Pass continue to evolve with each new disc.

BD+ needs a SVM to be implemented, but note that the Blu-ray specifications already include a VM requirement for the BD-Java feature. This BD-J feature can also be used to implement structural protection schemes such as Sony DADC's Screen Pass. In this scheme, BD-J code on the disc actively looks for signs of protection being in place during playback. When the BD-J code finds that the protection features are missing (say, due to playing an unprotected copy, or when ripping tools are active in the background), playback is immediately stopped along with an on-screen message. DVDFab's blog has some more details on Screen Pass.
In addition to DRMs aimed at directly protecting content by encryption, the Blu-ray developers also considered some watermarking schemes. Watermarking doesn't actually encrypt the content, but places some non-discernible (to the naked eyes/ears) information in the audio / video tracks of the stream. By serving as a digital signature, it helps the player / analyzer identify the content status. In the next section, we will be talking in detail about Cinavia, the audio watermarking scheme from Verance. Thomson's NexGuard is a type of video watermarking scheme which works with the help of the BD+ SVM. The BD+ content code embeds some invisible information in the video track which contains details of the player / drive used to decrypt the stream. If the video gets out and becomes a 'pirated copy', the watermark can be analyzed to determine the player / drive responsible for the 'piracy'. BD+ code in subsequent Blu-rays can be used to blacklist the player / add it to a revocation list.
If you are interested in learning more about content protection in Blu-rays, I strongly suggest perusing Chapter 4 of Blu-ray Disc Demystified.











121 Comments
View All Comments
medi01 - Wednesday, March 21, 2012 - link
It's been a while that companies do some shady stuff vs legit customers in the name of "fighting piracy", but it's depressing to see nobody notices. No LAN play "to fight piracy" by Blizzard (in fact, they simply wanted to have share of what Korean Starcraft channels earn), "you gotta be online to play this game" => say goodbye aftermarket.Oh, and the most hilarious "stuff recorded on this TV can only be played on this TV". Niiice. That will show them, the evil pirates with blue-ray rips. Remind me why do we still use HDMI with all the "advanced encryption"?
titanmiller - Wednesday, March 21, 2012 - link
How are consumers expected to update their firmware if they don't have home broadband internet?My parents live in a rural area and have to use a USB 3g internet provider. There isn't any easy way to connect their blu-ray player to the internet for it to download a firmware update.
gigahertz20 - Wednesday, March 21, 2012 - link
Screw all the ridiculous high prices for bluray movies, get a fat pipe internet connection and usenet provider and you're set. BTW, for those looking to ditch torrents and get into usenet, Astraweb has a new plan, $50 for 1TB of downloads. Of course, if you download a ton, then get the unlimited plan for $9-11 a month.andy o - Wednesday, March 21, 2012 - link
"Thomson's NexGuard is a type of video watermarking scheme which works with the help of the BD+ SVM. The BD+ content code embeds some invisible information in the video track which contains details of the player / drive used to decrypt the stream."I can't think of a blu-ray rip that would include this watermark. How could it, if the rip is not taken from the video feed, the file itself is decrypted with a drive that's not a BD-video drive (a proper BD player)? Am I missing something, or are they that clueless that they think people are pirating by connecting their players' video outputs to a VCR?
Farfle - Wednesday, March 21, 2012 - link
You forgot "or" in the title, right before the colon.p05esto - Wednesday, March 21, 2012 - link
I freaking HATE Cinavia protection. I ripped my entire DVD/BluRay library to digital MKV files (hundreds of movies) and have been using a Samsung 6500 BluRay player to stream the movies from my home server. I have three of those players in the house and everything had been awesome....until recently. About a month ago a recent firmware ADDED the Cinavia protection to the Samsung player and now many of my movies no longer play and I get those stupid Cinavia protection errors.Anandtech PLEASE raise hell, raise awarness about this evil technology. Consumers should be able to rip their old school discs to digital files without having to deal with horrid DRM getting in the way of enjoying a movie.
And a warning to users to stay away from Samsung. They crippled my devices a year after I bought them with this new Cinavia protection. They took away functionality and are evil bastards for doing so. I believe a lawsuit is in order, you can't sell a product and then a year later disable the main feature I use it for and get away with that crap. Who's with me???
Blibbax - Wednesday, March 21, 2012 - link
The industry sure does do an excellent job of making TPB more attractive.blowfish - Wednesday, March 21, 2012 - link
None of the shenanigans of the BDA surprise me - the industry is run by Shylocks, for whom money is everything.AbRASiON - Wednesday, March 21, 2012 - link
I hope so, I'm planning to move to XBMC (instead of my PS3) for this very reason over the coming months.ComputerGuy2006 - Thursday, March 22, 2012 - link
I took off my pants, bent over the table and allowed several sites JS access to my PC... and I still cant view the videos... Why not use utube?