Intel at Hot Chips 2018: Showing the Ankle of Cascade Lake
by Ian Cutress on August 19, 2018 7:30 PM EST- Posted in
- CPUs
- Intel
- Spectre
- AVX-512
- Meltdown
- Cascade Lake
- Optane DIMMs
- VNNI
The final presentation of the Hot Chips event this week is from Intel, with a talk on its next generation Xeon Scalable platform, Cascade Lake. We recently learned about Intel’s Xeon Roadmap at the recent Datacenter Insider Summit, consisting of Cascade Lake in 2018, Cooper Lake in 2019, and Ice Lake in 2020, and now Hot Chips is the first chance for Intel to add some more information to the mix. Previously this would have been done at events like IDF, over several hours, but Intel only has 30 minutes on stage here. We picked up the slides before the presentation.
The Key Takeaways
Intel is using the opportunity to expand on Cascade Lake’s previously announced features: new instructions for machine learning by taking advantage of the AVX-512 unit, and how the platform is set to be protected / hardened against attacks such as Spectre and Meltdown. We also have confirmation about how the new Optane DIMMs, Apache Pass, will be enabled through the platform.
Unfortunately, for those expecting an IDF-like substantial talk about the design of the chips, how the SKUs will be separated, or what the product stack will look like, this was not it. We have a feeling that Intel will be drip feeding information about Cascade Lake in this manner.
However, Intel’s main play here is that a significant amount of the server and enterprise industry desperately want Spectre and Meltdown hardened processors, and will pay for them. When Intel stated that they expect Cascade to be their fastest ramping processor, make no mistake that this is likely to be true, for the reasons of security. The question marks will obviously come on price, which has yet to be announced, but Intel could easily argue ‘how much is security worth?’.
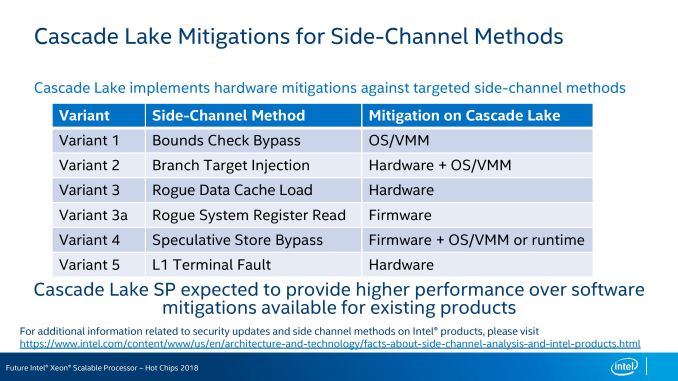
Protecting for Spectre, Meltdown, and Similar Attacks
With the range of new attacks, Intel and others moved quickly to enable firmware and operating system remedies. The downside of those remedies was a potential loss in performance, mainly due to kernel switching, that on the latest platforms could account for 3-10% performance (or more old older systems). When we spoke with Lisa Spelman, VP of Intel’s DCG, we were told that the hardware-based mitigations in Cascade Lake would have an impact on the performance loss – exactly how much was not stated, and we were told that ‘the comparison is sort of apples to oranges – either way performance is set to be increased [because of platform updates]’. Lisa did categorically state that ‘the hardware fixes put the performance back on track’, which is the key takeaway.
For the variants of side-channel attacks, Intel is applying the following updates to Cascade Lake:
Variant 1 is still to be tackled at the OS level, with variants 3a and 4 through firmware and OS updates. Variants 2, 3, and 5, will be solved in hardware, requiring no extra additions.
So while the new processors have fixes in place, not all of them will be hardware fixes. The firmware fixes might as well be hardware, given that the system will launch with these by default, but the OS fixes will have to be pushed before platforms are released. The non-hardware fixes have the potential for performance regression, however as stated above, the platform as a whole should be at a higher performance level than Skylake.
Intel did not state what the lead time was for different variant attacks to be added in hardware beyond Cascade Lake, however the earlier they know, the better. Lisa Spelman did state that every new processor features security updates, and the teams they have will be working hard to provide the best solution.
Page 2: Process Tuning and VNNI
Page 3: Optane DIMMs and Slides
Top image originally from ServeTheHome










31 Comments
View All Comments
HStewart - Monday, August 20, 2018 - link
It very possibility that Variant 1 is not volubility in the hardware designed but how OS developers use the code.GreenReaper - Monday, August 20, 2018 - link
Well, it's a problem for all software with secrets it wants to keep, and means of speculation involving access to them. The most common example of this is the OS/VMM.The core issue is that the speed of access to data is non-deterministic in the x86 model. Nothing in the original design said "you can't *try* to go faster than you would if you had to load everything only at the point that it came up" - indeed, doing so has been viewed as a feature for decades.
Meanwhile timing attacks have been viewed as relatively hard to exploit. But there are many ways in which a timing gadget may be constructed, this is arguably just a newly-discovered pattern commonly used by privileged software.
HStewart - Monday, August 20, 2018 - link
Unfortunately today we have increase of hackers that will try to take advantage of such features to hamper system. Which cause headaches for both CPU designers and OS designers.Also the following link as interesting statement about these attacks not being just Intel.
It actually states "This contradicts some early statements made about the Meltdown vulnerability as being Intel-only"
https://en.wikipedia.org/wiki/Meltdown_(security_v...
iwod - Monday, August 20, 2018 - link
When Zen 2 comes, which is going to be slightly later than CLake I think, please test Clake with all those security measures fix and see how it fare against AMD.moozooh - Monday, August 20, 2018 - link
So does this mean the Optane DIMMs won't be compatible with the consumer CPUs / chipset families? Cause I'd love to have it as a universal in-hardware RAM drive alternative with comparable latencies and IOPS performance but more convenience and far less compatibility issues.edzieba - Monday, August 20, 2018 - link
We've known that for quite some time: the Optane DIMMs require dedicated hardware in the processor (where the memory controllers are) which is only currently present in Xeon scalable CPUs.HStewart - Monday, August 20, 2018 - link
This is exactly wanted to here about the Spectrum - Meltdown stuff - we all know it that Intel has been under stress about this and the delay of 10nm - but some have reported that the hardware changes would be delay until 10nm - so this means that Intel does not have to have all 10nm to make those changes in hard. So 14nm++ or what every people is not same architecture as previous chips. To me it obvious that Intel has put fixing these security issues top priority.As for some of problems requiring OS/VMM - as a former OS developer, it very possible that volubility is in designed of OS - Intel has given OS developers like Microsoft, Apple - and unix base community software recommendations for changes in code to prevent them in current hard.
wpapolis - Monday, August 20, 2018 - link
“Showing the Ankle” and “drip feeding”? You r mixing your metaphors. You need to focus on one theme like ... “raising it’s skirt”, “showing more leg” ... u know ... like that! 👍 Another great article ... now let me get back to reading the rest! HahaKevin G - Monday, August 20, 2018 - link
Intel did do something tricky in that while LGA 3647 exposes 48 PCIe lanes, the HCC and XCC dies actually contain 64 lane PCIe controller. The 16 lanes are for on package accelerators or fabric. While I doubt Intel did increase this figures (or add an on-die UPI link), their wording appears to keep that possibility open.nirmal12 - Monday, October 8, 2018 - link
For those people expecting an IDF-like substantial talk about the chips. The question arising are how the SKUs will be separated, How product stack will look like etc. I also think Intel will be drip feeding information about Cascade Lake.