AMD's Future in Servers: New 7000-Series CPUs Launched and EPYC Analysis
by Ian Cutress on June 20, 2017 4:00 PM EST- Posted in
- CPUs
- AMD
- Enterprise CPUs
- EPYC
- Whitehaven
- 1P
- 2P
With recent fears about security, and given that these processors are aiming to go to the Enterprise space, AMD had to dedicate some time to explaining how secure the new platform is. AMD has had its Secure Processor in several CPUs at this point: a 32-bit ARM Cortex-A5 acting as a microcontroller that runs a secure OS/kernel with secure off-chip storage for firmware and data – this helps provide cryptographic functionality for secure key generation and key management. This starts with hardware validated boot (TPM), but includes Secure Memory Encryption and Secure Encrypted Virtualization.
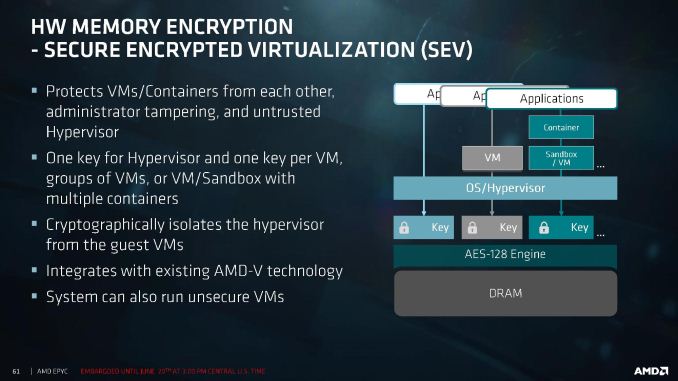
Encryption starts at the DRAM level, with an AES-128 engine directly attached to the MMU. This is designed to protect against physical memory attacks, with each VM and Hypervisor able to generate a separate key for their environment. The OS or Hypervisor can choose which pages to encrypt via page tables, and the DMA engines can provide support for external devices such as network storage and graphics cards to access encrypted pages.
Because each VM or container can obtain its own encryption key, this isolates them from each other, protecting against cross-contamination. It also allows unencrypted VMs to run alongside encrypted ones, removing the all-or-nothing scenario. The keys are transparent to the VMs themselves, managed by the protected hypervisor. It all integrates with existing AMD-V technology.
Alongside this are direct RAS features in the core, with the L1 data cache using SEC-DED ECC and L2/L3 caches using DEC-TED ECC. The DRAM support involves x4 DRAM device failure correction with addr/cmd parity and write CRC with replay. Data poisoning is handled with reporting and a machine check recovery mode. The Infinity Fabric between dies and between sockets is also link-packet CRC backed with retry.
One element that was not discussed is live VM migration across encrypted environments. We fully suspect that an AMD-to-AMD live migration be feasible, although an AMD-to-Intel or Intel-to-AMD will have issues, given that each microarchitecture has unique implementations of certain commands.










131 Comments
View All Comments
yuhong - Tuesday, June 20, 2017 - link
"Linus kernel"IanHagen - Tuesday, June 20, 2017 - link
Linux Tech Tips?Krysto - Tuesday, June 20, 2017 - link
That Linux guy makes some great videos.thomasg - Tuesday, June 27, 2017 - link
Believe it or not - for the older guys here the more well known Linus is Linus Torvalds, the creater of Linux (after whom it is named), not a YouTuber.For those that freudian typo isn't quite that hilarious.
Guspaz - Tuesday, June 20, 2017 - link
sudo modprobe socks_sandalsHollyJordan - Wednesday, June 21, 2017 - link
Do you have a pay_pal ? because you can generate an extra 1000 /week in your earnings only working at home for five hours a day... check.philehidiot - Tuesday, June 27, 2017 - link
Ooooh, I have Pay Pal and I'd love to earn 1000 Tasmanian Pesos a week for 5 hours a day from the comfort of my own home.I can imagine that would work out as all of $4/month.
OddFriendship8989 - Wednesday, June 28, 2017 - link
How about 1000 Bitcoins?satai - Tuesday, June 20, 2017 - link
1 socket 16 / 32 @ 2.9GHz max for $700+... it looks like 16 core Threadripper with reasonable frequencies for less then $999 looks reasonable.spikebike - Tuesday, June 20, 2017 - link
Typically desktop/workstation chips have higher clocks and less cores than the pure servers. But I'd be really surprised if the threadripper isn't significantly cheaper than the Epyc. Keep in mind a thread ripper has half the silicon dies, half the memory channels, and half the pci-e of the Epyc.